NGINX Node Artifact Versions and Changelog¶
This document lists available versions of the NGINX Wallarm Node 6.x in various form factors, helping you track releases and plan upgrades.
All-in-one installer¶
Since version 4.10, installation and upgrading of Wallarm nodes is performed only with all all-in-one installer. Manual upgrade with individual Linux packages is not supported anymore.
History of all-in-one installer updates simultaneously applies to it's x86_64 and ARM64 versions.
How to migrate from DEB/RPM packages
How to migrate from previous all-in-one installer version
6.12.3 (2026-05-25)¶
-
Added BoringSSL compatibility — the Wallarm NGINX module can now run on BoringSSL-linked NGINX builds. JA4 TLS fingerprinting and encrypted upstream traffic to the postanalytics service are disabled when the build lacks the required symbols
-
Fixed the HEX parser producing false detections on very short alphanumeric inputs such as two-character values
-
Fixed HEX-encoded points in serialized requests causing parsing errors in the postanalytics service and API Discovery
-
Fixed API Discovery inferring the wrong content type for responses — the value is now read from request-level metadata instead of the response
Content-Typeheader -
Fixed gRPC and WebSocket responses being blocked on detected infoleaks
6.12.2 (2026-05-19)¶
-
Added support for NGINX stable 1.30.1
-
Added support for NGINX mainline 1.31.0
To mitigate the risk of the NGINX vulnerabilities CVE-2026-42945, CVE-2026-42946, CVE-2026-40460, CVE-2026-42934, and CVE-2026-40701, upgrade NGINX to stable 1.30.1 or mainline 1.31.0 and update Wallarm Node to 6.12.2.
6.12.1 (2026-05-12)¶
-
Added full support for the ME (Middle East) Wallarm Cloud in the all-in-one installer:
- Interactive mode now lists ME Cloud alongside the US and EU options.
- The
-c, --cloudflag now acceptsMEas a value. - The
-H, --hostflag description now referencesme1.api.wallarm.com.
6.12.0 (2026-05-04)¶
-
Added support for MCP server discovery in API Discovery
-
Added support for MCP Sessions
-
Added MCP mitigation controls: ACL policy, request verification, and tool input schema enforcement
-
Added HEX encoding attack detection — the Node now decodes and analyzes HEX-encoded payloads, improving protection against obfuscation-based bypass techniques
-
Added per-tenant statistics and logging in multi-tenant deployments:
- The
wallarm_partner_client_uuiddirective now accepts an optional human-readable label - Two new NGINX variables (
$wallarm_partner_client_uuid,$wallarm_partner_client_label) are available for use in extended log formats - The
wallarm_statusendpoint now includes per-tenant traffic breakdown in both JSON and Prometheus output formats — per-application (wallarm_*_per_app_totalmetrics) and per-group (wallarm_*_per_group_totalmetrics) via thewallarm_status_groupdirective
- The
-
Added
?format=jsonand?format=prometheusquery parameter support to thewallarm_statusendpoint, allowing the output format to be overridden at request time -
Fixed API Specification Enforcement incorrectly reporting requests as "undefined endpoint" for OpenAPI specs that define a base path in the
serversblock -
Bumped Go version to 1.26.1
6.11.3 (2026-04-29)¶
-
Added support for NGINX mainline 1.29.8
-
Added support for NGINX stable 1.30.0
-
Fixed intermittent errors in custom ruleset loading and GraphQL processing
-
Fixed NGINX worker crash (signal 11) when serving custom blocking pages configured via file path while response header modification rules were active
6.11.2 (2026-03-27)¶
- Added compatibility with latest NGINX versions shipped by RHEL-based distros
6.11.1 (2026-03-25)¶
-
Added support for NGINX stable 1.28.3
-
Added support for NGINX mainline 1.29.7
6.11.0 (2026-03-25)¶
-
Added authentication flow detection in API Discovery — automatically identifies authentication methods used by each endpoint and highlights unauthenticated endpoints
-
Fixed empty response (
000status code) instead of custom block page whenngx_http_auth_request_moduleis used -
Fixed the GHSA-6g7g-w4f8-9c9x vulnerability
-
Bumped Go version to 1.26.1
6.10.3 (2026-03-16)¶
- Fixed a memory leak in the API Specification Enforcement component that caused steadily increasing memory consumption and eventual OOMKill pod restarts
6.10.2 (2026-03-10)¶
-
Added new traffic metrics to the
wallarm-statusstatistics service:bytes_blocked_in,bytes_blocked_out,bytes_blocked_by_acl_in, andbytes_blocked_by_acl_outThese counters track the volume of incoming and outgoing traffic in blocked requests, split by block reason (attack/overlimit/antibot vs. denylists). Available in JSON, Prometheus, and per-application split formats.
-
Fixed a shared memory allocation bug in the statistics service initialization that could lead to data corruption under high load
-
Fixed memory limit handling for wcli jobs
-
Fixed security vulnerabilities:
6.10.1 (2026-02-18)¶
- Added support for circular references in OpenAPI specifications uploaded for API Specification Enforcement
6.10.0 (2026-02-09)¶
-
Added support for OpenAPI v3 specifications with non-string (for example, integer) YAML keys in API Specification Enforcement. This improves compatibility and prevents schema parsing failures
-
Added support for NGINX stable 1.28.2
-
Fixed an issue where the Node sent too many requests in a single batch to wstore, causing submission failures
6.9.0 (2026-01-15)¶
-
Increased the frequency of session updates sent to the Wallarm Cloud. Sessions now appear in the UI faster, closer to real time
-
Improved memory usage monitoring and prevention of resource exhaustion
-
Added support for NGINX stable 1.28.1
-
Fixed the CVE-2026-21441 vulnerability
6.8.1 (2025-12-24)¶
-
Fixed an issue where malformed fuzzing traffic could cause NGINX crashes, as observed in logs
-
Added API token masking in Node logs to prevent sensitive data exposure
6.8.0 (2025-12-23)¶
- Bug fixes:
- Fixed the issue where integers were not being masked when using the "Mask sensitive data" rule
- Fixed the issue where responses containing infoleak stamps were being blocked. Wallarm no longer blocks such responses, as doing so caused false detections and prevented rules from being edited
- Fixed the issue where the
wallarm_statusservice statistics contained the outdatedabnormalmetric, which was incorrectly increasing with each request. The metric and other outdated fields have been removed
6.7.3 (2025-12-11)¶
- Fixed an issue where large or overlapping denylisted IP ranges were not being blocked in Security Edge-hosted environments
6.7.1 (2025-11-17)¶
- Fixed
'error: no error'when processing gRPC/WebSocket response attacks
6.7.0 (2025-11-05)¶
-
Node installation now requires that no system user named
wallarmexists -
Added support for Ubuntu 25.10 (Questing Quokka)
-
Added support for CentOS 10 Stream
-
Added support for Oracle Linux 10.x
-
Added support for NGINX mainline 1.29.2 and 1.29.3
-
Updated AlmaLinux 9 support to include the latest package updates
-
Introduced JA4 fingerprinting in the NGINX node
JA4 fingerprints help detect threats and malicious clients based on TLS handshake characteristics. JA4 fingerprints are used as an additional factor when deciding to block a request.
The feature is disabled by default. To enable it, add the following NGINX directive inside the
httporserverblock: -
Introduced the
wallarm_fingerprint_ja4_rawandwallarm_fingerprint_ja4variables to configure extended logging when JA4 fingerprinting is enabled -
Improved Node initialization logs — added detailed information about component type, supported versions, error source, API endpoint, and Node UUID to simplify troubleshooting during the initialization stage
-
Fixed the CVE-2025-58188 vulnerability
-
Fixed the issue where the Node raised an error when a JWT token was sent in the
Authorization: Bearerheader -
Fixed invalid type error when editing automatically created rules for attacks detected in gRPC responses
6.6.1 (2025-10-16)¶
-
Introduced support for OpenAPI 3.1 in the API Specification Enforcement feature — you can now upload specifications in version 3.1 format to compare traffic against them, identify mismatches, and mitigate related security risks
-
Fixed the following vulnerabilities:
6.6.0 (2025-10-03)¶
-
Changed the default wstore binding to IPv4 (
tcp4), it now listens only on IPv4 instead of dual‑stackIf your configuration uses
localhostfor wstore, update it to127.0.0.1. -
Introduced protocol selection (tcp, tcp4, tcp6) using the
WALLARM_WSTORE__SERVICE__PROTOCOLenvironment variable, which can be set in/opt/wallarm/env.listThe default value is
"tcp4". -
Fixed an issue where response context parameters configured in API Sessions were not uploaded to the Wallarm Cloud
-
Introduced a new Prometheus metric
wallarm_wcli_job_export_periodto track the average export delay for each wcli job (e.g.,reqexp,blkexp,botexp) -
Introduced a new
$wallarm_modevariable for extended loggingThis variable returns the final filtration mode applied to a malicious request, taking into account both local settings and those from the Wallarm Cloud (e.g., rules and mitigation controls) with their prioritization.
-
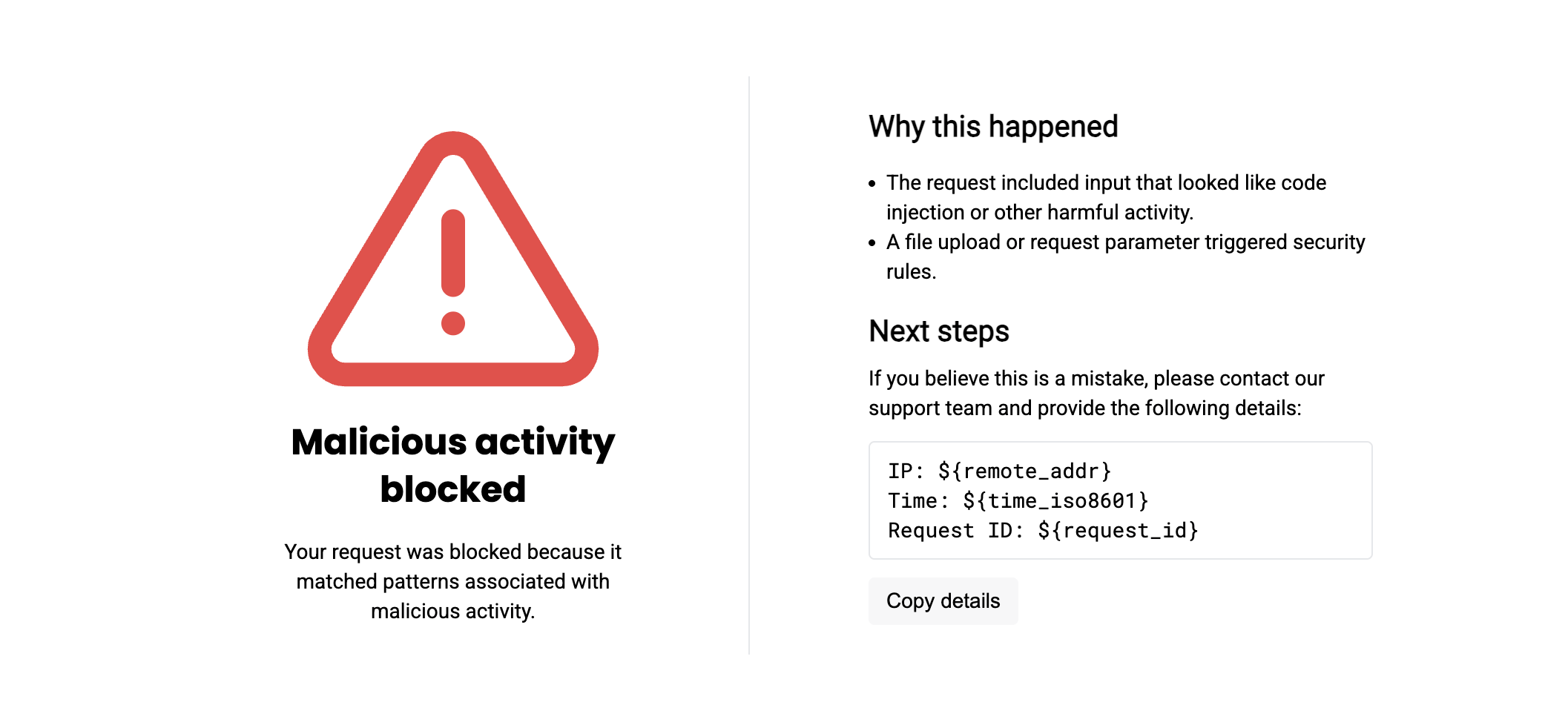
Updated the wording on the Wallarm-branded block page, the page now looks as follows:
6.5.1 (2025-09-09)¶
-
Added support for blocking attackers by API sessions
-
Added support for NGINX Plus R35
-
Exposed wcli Controller metrics endpoint for external monitoring
-
Relaxed content-type validation in API Specification Enforcement: requests with image MIME types (
image/png,image/jpeg,image/gif,image/webp,image/avif,image/heic,image/heif,image/bmp,image/tiff,image/svg+xml) are no longer rejected -
Bumped Go version to 1.24
-
Fixed the behavior of the
wallarm_wstore_throttle_modePrometheus metric, which previously did not return to the normal state (0) after throttling ended
6.4.1 (2025-08-07)¶
-
Added Prometheus metrics support for API Specification Enforcement service operation (based on the built-in API Firewall service):
- Enable with
APIFW_METRICS_ENABLED=truein/opt/wallarm/env.list - Default endpoint:
:9010/metrics - Host and endpoint name configurable via variables
APIFW_METRICS_HOSTandAPIFW_METRICS_ENDPOINT_NAME
- Enable with
6.4.0 (2025-07-31)¶
-
Introduced a new
wallarm_block_reasonvariable for extended loggingThis variable adds to the log an information on reason of request blocking (detected attack, part of bot activity, Denylist etc.)
-
Introduced the new
wallarm_export_streamsWallarm directive which controls whether the Node exports information about long-lived streaming connections to the internal postanalytics storage (wstore)By default,
wallarm_export_streamsis set tooff. When enabled, the Node sends stream and message data to wstore, allowing API Discovery to build the API inventory and display gRPC/WebSocket endpoints in the Wallarm Console UI. -
Fixed the stuffed credentials export to the Cloud
-
Improved GraphQL parser
-
Bug fixes and internal improvements
6.3.1 (2025-07-23)¶
- Fixed memory leak
6.3.0 (2025-07-08)¶
-
Added support for file upload restriction policy via mitigation controls
-
Added support for unrestricted resource consumption mitigation by API Abuse Prevention
-
In rules, the separator used in xml_tag values that combine a URI, namespace, and tag name has been changed from
:to| -
Internal improvements
6.2.1 (2025-06-23)¶
- Minor internal file structure change
6.2.0 (2025-06-20)¶
-
Added support for mitigation control-based GraphQL API Protection
-
Optimized stream handling for gRPC traffic
-
Added the
streamsandmessagesparameters to the/wallarm-statusservice output to report the number of processed gRPC/WebSocket streams and messages -
Added support for SSL/TLS and mTLS between the NGINX-Wallarm module and the postanalytics module when they are installed separately
-
Fixed wstore ports binding: now bound to
127.0.0.1instead of0.0.0.0 -
Minor bug fixes
6.1.0 (2025-05-09)¶
-
Added support for enumeration mitigation controls
-
Added support for DoS protection mitigation control
-
Bugfix: Attacks originated from allowlisted sources are no longer shown in the Attacks section
-
wstore logs now include
"component": "wstore"for easier identification
6.0.3 (2025-05-07)¶
-
Added support for Amazon Linux 2
-
Fixed the installation issues with custom NGINX
6.0.2 (2025-04-29)¶
-
Added support for NGINX stable 1.28.0
-
Added support for NGINX mainline 1.27.5
6.0.1 (2025-04-22)¶
- Fixed the CVE-2024-56406, CVE-2025-31115 vulnerabilities
6.0.0 (2025-04-03)¶
-
Initial release 6.0, see changelog
-
Added support for NGINX Plus R34
Helm chart for Wallarm NGINX Ingress controller¶
6.12.3 (2026-05-25)¶
-
Added BoringSSL compatibility — the Wallarm NGINX module can now run on BoringSSL-linked NGINX builds. JA4 TLS fingerprinting and encrypted upstream traffic to the postanalytics service are disabled when the build lacks the required symbols
-
Fixed the HEX parser producing false detections on very short alphanumeric inputs such as two-character values
-
Fixed HEX-encoded points in serialized requests causing parsing errors in the postanalytics service and API Discovery
-
Fixed API Discovery inferring the wrong content type for responses — the value is now read from request-level metadata instead of the response
Content-Typeheader -
Fixed gRPC and WebSocket responses being blocked on detected infoleaks
6.12.2 (2026-05-19)¶
- Pulled in a curl/libcurl security patch from the Alpine base image: CVE-2026-3805.
6.12.1 (2026-05-12)¶
-
Added optional human-readable label support to the
nginx.ingress.kubernetes.io/wallarm-partner-client-uuidannotation, aligning it with thewallarm_partner_client_uuiddirective (added in NGINX Node 6.12.0)Pass the UUID and label as a space-separated value:
"<UUID> <LABEL>".
6.12.0 (2026-05-04)¶
-
Added support for MCP server discovery in API Discovery
-
Added support for MCP Sessions
-
Added MCP mitigation controls: ACL policy, request verification, and tool input schema enforcement
-
Added HEX encoding attack detection — the Node now decodes and analyzes HEX-encoded payloads, improving protection against obfuscation-based bypass techniques
-
Added per-tenant statistics and logging in multi-tenant deployments:
- The
wallarm_partner_client_uuiddirective now accepts an optional human-readable label - Two new NGINX variables (
$wallarm_partner_client_uuid,$wallarm_partner_client_label) are available for use in extended log formats - The
wallarm_statusendpoint now includes per-tenant traffic breakdown in both JSON and Prometheus output formats — per-application (wallarm_*_per_app_totalmetrics) and per-group (wallarm_*_per_group_totalmetrics) via thewallarm_status_groupdirective
- The
-
Added
?format=jsonand?format=prometheusquery parameter support to thewallarm_statusendpoint, allowing the output format to be overridden at request time -
Fixed API Specification Enforcement incorrectly reporting requests as "undefined endpoint" for OpenAPI specs that define a base path in the
serversblock -
Bumped Go version to 1.26.1
-
Fixed security vulnerabilities:
6.11.3 (2026-04-29)¶
-
Fixed intermittent errors in custom ruleset loading and GraphQL processing
-
Fixed NGINX worker crash (signal 11) when serving custom blocking pages configured via file path while response header modification rules were active
6.11.2 (2026-03-27)¶
- Internal improvements
6.11.1 (2026-03-25)¶
-
Added authentication flow detection in API Discovery — automatically identifies authentication methods used by each endpoint and highlights unauthenticated endpoints
-
Upgraded to Community Ingress NGINX Controller version 1.15.0, aligning with the upstream Helm chart version 4.15.0
The underlying NGINX has been updated to 1.27.1 and the base Alpine image to 3.23.3.
Supported Kubernetes versions are now 1.31–1.35.
-
Fixed empty response (
000status code) instead of custom block page whenngx_http_auth_request_moduleis used -
Fixed the GHSA-6g7g-w4f8-9c9x vulnerability
-
Bumped Go version to 1.26.1
6.10.3 (2026-03-16)¶
- Fixed a memory leak in the API Specification Enforcement component that caused steadily increasing memory consumption and eventual OOMKill pod restarts
6.10.2 (2026-03-10)¶
-
Added new traffic metrics to the
wallarm-statusstatistics service:bytes_blocked_in,bytes_blocked_out,bytes_blocked_by_acl_in, andbytes_blocked_by_acl_outThese counters track the volume of incoming and outgoing traffic in blocked requests, split by block reason (attack/overlimit/antibot vs. denylists). Available in JSON, Prometheus, and per-application split formats.
-
Fixed a shared memory allocation bug in the statistics service initialization that could lead to data corruption under high load
-
Fixed memory limit handling for wcli jobs
-
Fixed security vulnerabilities:
6.10.1 (2026-02-18)¶
- Added support for circular references in OpenAPI specifications uploaded for API Specification Enforcement
6.10.0 (2026-02-09)¶
-
Added support for OpenAPI v3 specifications with non-string (for example, integer) YAML keys in API Specification Enforcement. This improves compatibility and prevents schema parsing failures
-
Fixed an issue where the Node sent too many requests in a single batch to wstore, causing submission failures
6.9.0 (2026-01-15)¶
-
Increased the frequency of session updates sent to the Wallarm Cloud. Sessions now appear in the UI faster, closer to real time
-
Improved memory usage monitoring and prevention of resource exhaustion
-
Fixed the CVE-2026-21441 vulnerability
6.8.1 (2025-12-24)¶
-
Fixed an issue where malformed fuzzing traffic could cause NGINX crashes, as observed in logs
-
Added API token masking in Node logs to prevent sensitive data exposure
6.8.0 (2025-12-23)¶
- Bug fixes:
- Fixed the issue where integers were not being masked when using the "Mask sensitive data" rule
- Fixed the issue where responses containing infoleak stamps were being blocked. Wallarm no longer blocks such responses, as doing so caused false detections and prevented rules from being edited
- Fixed the issue where the
wallarm_statusservice statistics contained the outdatedabnormalmetric, which was incorrectly increasing with each request. The metric and other outdated fields have been removed
6.7.3 (2025-12-11)¶
- Fixed an issue where large or overlapping denylisted IP ranges were not being blocked in Security Edge-hosted environments
6.7.1 (2025-11-17)¶
-
Fixed YAML indentation issue causing Helm deployment to fail when postanalytics was configured as a DaemonSet
-
Fixed
'error: no error'when processing gRPC/WebSocket response attacks
6.7.0 (2025-11-05)¶
-
Updated Community Ingress NGINX Controller 1.11.8 support to align with the latest upstream updates
-
Introduced JA4 fingerprinting in the NGINX node
JA4 fingerprints help detect threats and malicious clients based on TLS handshake characteristics. JA4 fingerprints are used as an additional factor when deciding to block a request.
The feature is disabled by default. To enable it, add the following NGINX directive inside the
httporserverblock: -
Introduced the
wallarm_fingerprint_ja4_rawandwallarm_fingerprint_ja4variables to configure extended logging when JA4 fingerprinting is enabled -
Improved Node initialization logs — added detailed information about component type, supported versions, error source, API endpoint, and Node UUID to simplify troubleshooting during the initialization stage
-
Updated default values for wcli Controller metrics:
-
Switched to native HTTP readiness and liveness probes for the wstore component
-
Fixed the following vulnerabilities:
-
Fixed the issue where the Node raised an error when a JWT token was sent in the
Authorization: Bearerheader -
Fixed invalid type error when editing automatically created rules for attacks detected in gRPC responses
6.6.2 (2025-10-16)¶
-
Introduced support for OpenAPI 3.1 in the API Specification Enforcement feature — you can now upload specifications in version 3.1 format to compare traffic against them, identify mismatches, and mitigate related security risks
-
Fixed the following vulnerabilities:
6.6.1 (2025-10-08)¶
-
Fixed the postanalytics (wstore) liveness probe to align with the
serviceProtocolsettingWhen
serviceProtocolis set totcp4, the probe now explicitly uses IPv4, preventing restarts for dual-stack/IPv6 clusters.
6.6.0 (2025-10-03)¶
-
Changed the default wstore binding to IPv4 (
tcp4), it now listens only on IPv4 instead of dual‑stack -
Introduced protocol selection (tcp, tcp4, tcp6) in Ingress values (
controller.wallarm.postanalytics.serviceProtocol)The default value is
"tcp4". -
Changed the default value of
controller.wallarm.postanalytics.serviceAddressto"0.0.0.0:3313"This allows IPv4 traffic only. If you are using a custom value, make sure it matches the selected
controller.wallarm.postanalytics.serviceProtocol. -
Fixed an issue where response context parameters configured in API Sessions were not uploaded to the Wallarm Cloud
-
Introduced a new Prometheus metric
wallarm_wcli_job_export_lagto track the average export delay for each wcli job (e.g.,reqexp,blkexp,botexp) -
Introduced a new
wallarm_modevariable for extended loggingThis variable returns the final filtration mode applied to a malicious request, taking into account both local settings and those from the Wallarm Cloud (e.g., rules and mitigation controls) with their prioritization.
-
Updated the wording on the Wallarm-branded block page, the page now looks as follows:
-
Fixed the following vulnerabilities:
6.5.1 (2025-09-09)¶
-
Added support for blocking attackers by API sessions
-
Added Prometheus metrics support for API Specification Enforcement service operation (based on the built-in API Firewall service)
Metrics are disabled by default and can be enabled through the new
controller.wallarm.apiFirewall.metrics.*values. -
Exposed wcli Controller metrics endpoint for external monitoring
-
Relaxed content-type validation in API Specification Enforcement: requests with image MIME types (
image/png,image/jpeg,image/gif,image/webp,image/avif,image/heic,image/heif,image/bmp,image/tiff,image/svg+xml) are no longer rejected -
Bumped Go version to 1.24
-
Fixed the behavior of the
wallarm_wstore_throttle_modePrometheus metric, which previously did not return to the normal state (0) after throttling ended -
Upgraded to Community Ingress NGINX Controller version 1.11.8, aligning with the upstream Helm chart version 4.11.8 and Alpine version 3.22.0
-
Fixed the CVE-2025-5399 and CVE-2025-22872 vulnerabilities due to the upstream upgrade
6.4.0 (2025-07-31)¶
-
Introduced a new
wallarm_block_reasonvariable for extended loggingThis variable adds to the log an information on reason of request blocking (detected attack, part of bot activity, Denylist etc.)
-
Introduced the new
wallarm_export_streamsWallarm directive which controls whether the Node exports information about long-lived streaming connections to the internal postanalytics storage (wstore)By default,
wallarm_export_streamsis set tooff. When enabled, the Node sends stream and message data to wstore, allowing API Discovery to build the API inventory and display gRPC/WebSocket endpoints in the Wallarm Console UI. -
Fixed the stuffed credentials export to the Cloud
-
Improved GraphQL parser
-
Bug fixes and internal improvements
6.3.1 (2025-07-23)¶
- Fixed memory leak
6.3.0 (2025-07-08)¶
-
Added support for file upload restriction policy via mitigation controls
-
Added support for unrestricted resource consumption mitigation by API Abuse Prevention
-
Added the
validation.forbidDangerousAnnotationschart value to toggle the CEL rule that blocks the dangerousserver-snippetandconfiguration-snippetannotationsBy default, it is set to
false- dangerous annotations are not blocked.Behaviour in Node 6.2.0- unchanged (annotations are blocked by default when
validation.enableCelistrue). -
Added support for the
controller.wallarm.postanalytics.serviceAddressparameter to customize the address and port for incoming wstore connections -
In rules, the separator used in xml_tag values that combine a URI, namespace, and tag name has been changed from
:to| -
Internal improvements
6.2.0 (2025-06-20)¶
-
Added support for mitigation control-based GraphQL API Protection
-
Optimized stream handling for gRPC traffic
-
Optimized stream handling for gRPC traffic
-
Added the
streamsandmessagesparameters to the/wallarm-statusservice output to report the number of processed gRPC/WebSocket streams and messages -
Added support for SSL/TLS and mTLS between the Filtering Node and the postanalytics module
-
Split the unified
controller.wallarm.wclicomponent invalues.yamlinto 2 separately configurable units:wcliControllerandwcliPostanalytics, allowing fine-grained control over containers -
Minor bug fixes
6.1.0 (2025-05-09)¶
-
Bugfix: Attacks originated from allowlisted sources are no longer shown in the Attacks section
-
wstore logs now include
"component": "wstore"for easier identification
6.0.2 (2025-04-25)¶
- Added the
validation.enableCelparameter to enable validation of Ingress resources via Validating Admission Policies
6.0.1 (2025-04-22)¶
- Fixed the CVE-2025-22871 vulnerability
6.0.0 (2025-04-03)¶
- Initial release 6.0, see changelog
Helm chart for Sidecar¶
6.12.3 (2026-05-25)¶
-
Added BoringSSL compatibility — the Wallarm NGINX module can now run on BoringSSL-linked NGINX builds. JA4 TLS fingerprinting and encrypted upstream traffic to the postanalytics service are disabled when the build lacks the required symbols
-
Fixed the HEX parser producing false detections on very short alphanumeric inputs such as two-character values
-
Fixed HEX-encoded points in serialized requests causing parsing errors in the postanalytics service and API Discovery
-
Fixed API Discovery inferring the wrong content type for responses — the value is now read from request-level metadata instead of the response
Content-Typeheader -
Fixed gRPC and WebSocket responses being blocked on detected infoleaks
6.12.2 (2026-05-19)¶
- Pulled in NGINX security patches from the base image: CVE-2026-42945, CVE-2026-42946, CVE-2026-40460, CVE-2026-42934, and CVE-2026-40701.
6.12.1 (2026-05-12)¶
- Internal improvements
6.12.0 (2026-05-04)¶
-
Added support for MCP server discovery in API Discovery
-
Added support for MCP Sessions
-
Added MCP mitigation controls: ACL policy, request verification, and tool input schema enforcement
-
Added HEX encoding attack detection — the Node now decodes and analyzes HEX-encoded payloads, improving protection against obfuscation-based bypass techniques
-
Added per-tenant statistics and logging in multi-tenant deployments:
- The
wallarm_partner_client_uuiddirective now accepts an optional human-readable label - Two new NGINX variables (
$wallarm_partner_client_uuid,$wallarm_partner_client_label) are available for use in extended log formats - The
wallarm_statusendpoint now includes per-tenant traffic breakdown in both JSON and Prometheus output formats — per-application (wallarm_*_per_app_totalmetrics) and per-group (wallarm_*_per_group_totalmetrics) via thewallarm_status_groupdirective
- The
-
Added
?format=jsonand?format=prometheusquery parameter support to thewallarm_statusendpoint, allowing the output format to be overridden at request time -
Fixed API Specification Enforcement incorrectly reporting requests as "undefined endpoint" for OpenAPI specs that define a base path in the
serversblock -
Bumped Go version to 1.26.1
-
Fixed the CVE-2026-34743 security vulnerability
6.11.3 (2026-04-29)¶
-
Fixed intermittent errors in custom ruleset loading and GraphQL processing
-
Fixed NGINX worker crash (signal 11) when serving custom blocking pages configured via file path while response header modification rules were active
6.11.2 (2026-03-27)¶
-
Bump Alpine version to 3.23
-
Upgrade NGINX to version 1.28.3
6.11.1 (2026-03-25)¶
-
Added authentication flow detection in API Discovery — automatically identifies authentication methods used by each endpoint and highlights unauthenticated endpoints
-
Fixed empty response (
000status code) instead of custom block page whenngx_http_auth_request_moduleis used -
Fixed the GHSA-6g7g-w4f8-9c9x vulnerability
-
Bumped Go version to 1.26.1
6.10.3 (2026-03-16)¶
- Fixed a memory leak in the API Specification Enforcement component that caused steadily increasing memory consumption and eventual OOMKill pod restarts
6.10.2 (2026-03-10)¶
-
Added new traffic metrics to the
wallarm-statusstatistics service:bytes_blocked_in,bytes_blocked_out,bytes_blocked_by_acl_in, andbytes_blocked_by_acl_outThese counters track the volume of incoming and outgoing traffic in blocked requests, split by block reason (attack/overlimit/antibot vs. denylists). Available in JSON, Prometheus, and per-application split formats.
-
Fixed a shared memory allocation bug in the statistics service initialization that could lead to data corruption under high load
-
Fixed memory limit handling for wcli jobs
-
Fixed security vulnerabilities:
6.10.1 (2026-02-18)¶
- Added support for circular references in OpenAPI specifications uploaded for API Specification Enforcement
6.10.0 (2026-02-09)¶
-
Added support for OpenAPI v3 specifications with non-string (for example, integer) YAML keys in API Specification Enforcement. This improves compatibility and prevents schema parsing failures
-
Fixed an issue where the Node sent too many requests in a single batch to wstore, causing submission failures
6.9.0 (2026-01-15)¶
-
Increased the frequency of session updates sent to the Wallarm Cloud. Sessions now appear in the UI faster, closer to real time
-
Improved memory usage monitoring and prevention of resource exhaustion
-
Fixed the CVE-2026-21441 vulnerability
6.8.1 (2025-12-24)¶
-
Fixed an issue where malformed fuzzing traffic could cause NGINX crashes, as observed in logs
-
Added API token masking in Node logs to prevent sensitive data exposure
6.8.0 (2025-12-23)¶
- Bug fixes:
- Fixed the issue where integers were not being masked when using the "Mask sensitive data" rule
- Fixed an issue where large or overlapping denylisted IP ranges were not being blocked in Security Edge-hosted environments
- Fixed the issue where responses containing infoleak stamps were being blocked. Wallarm no longer blocks such responses, as doing so caused false detections and prevented rules from being edited
- Fixed the issue where the
wallarm_statusservice statistics contained the outdatedabnormalmetric, which was incorrectly increasing with each request. The metric and other outdated fields have been removed
6.7.1 (2025-11-17)¶
- Fixed
'error: no error'when processing gRPC/WebSocket response attacks
6.7.0 (2025-11-05)¶
-
Introduced JA4 fingerprinting in the NGINX node
JA4 fingerprints help detect threats and malicious clients based on TLS handshake characteristics. JA4 fingerprints are used as an additional factor when deciding to block a request.
The feature is disabled by default. To enable it, add the following NGINX directive inside the
httporserverblock: -
Introduced the
wallarm_fingerprint_ja4_rawandwallarm_fingerprint_ja4variables to configure extended logging when JA4 fingerprinting is enabled -
Improved Node initialization logs — added detailed information about component type, supported versions, error source, API endpoint, and Node UUID to simplify troubleshooting during the initialization stage
-
Fixed the CVE-2025-58188 vulnerability
-
Fixed the issue where the Node raised an error when a JWT token was sent in the
Authorization: Bearerheader -
Fixed invalid type error when editing automatically created rules for attacks detected in gRPC responses
6.6.1 (2025-10-16)¶
-
Introduced support for OpenAPI 3.1 in the API Specification Enforcement feature — you can now upload specifications in version 3.1 format to compare traffic against them, identify mismatches, and mitigate related security risks
-
Fixed the following vulnerabilities:
6.6.0 (2025-10-03)¶
-
Changed the default wstore binding to IPv4 (
tcp4), it now listens only on IPv4 instead of dual‑stack -
Introduced protocol selection (tcp, tcp4, tcp6) in Ingress values (
postanalytics.wstore.config.serviceProtocol)The default value is
"tcp4". -
Changed the default value of
postanalytics.wstore.config.serviceAddressto"0.0.0.0:3313"This allows IPv4 traffic only. If you are using a custom value, make sure it matches the selected
postanalytics.wstore.config.serviceProtocol. -
Fixed an issue where response context parameters configured in API Sessions were not uploaded to the Wallarm Cloud
-
Introduced a new Prometheus metric
wallarm_wcli_job_export_lagto track the average export delay for each wcli job (e.g.,reqexp,blkexp,botexp) -
Introduced a new
$wallarm_modevariable for extended loggingThis variable returns the final filtration mode applied to a malicious request, taking into account both local settings and those from the Wallarm Cloud (e.g., rules and mitigation controls) with their prioritization.
-
Updated the wording on the Wallarm-branded block page, the page now looks as follows:
-
Fixed the following vulnerabilities:
6.5.1 (2025-09-09)¶
-
Added support for blocking attackers by API sessions
-
Added Prometheus metrics support for API Specification Enforcement service operation (based on the built-in API Firewall service)
Metrics are disabled by default and can be enabled through the new
config.wallarm.apiFirewall.metrics.*values. -
Exposed wcli Controller metrics endpoint for external monitoring
-
Relaxed content-type validation in API Specification Enforcement: requests with image MIME types (
image/png,image/jpeg,image/gif,image/webp,image/avif,image/heic,image/heif,image/bmp,image/tiff,image/svg+xml) are no longer rejected -
Bumped Go version to 1.24
-
Fixed the behavior of the
wallarm_wstore_throttle_modePrometheus metric, which previously did not return to the normal state (0) after throttling ended
6.4.0 (2025-07-31)¶
-
Introduced a new
wallarm_block_reasonvariable for extended loggingThis variable adds to the log an information on reason of request blocking (detected attack, part of bot activity, Denylist etc.)
-
Introduced the new
wallarm_export_streamsWallarm directive which controls whether the Node exports information about long-lived streaming connections to the internal postanalytics storage (wstore)By default,
wallarm_export_streamsis set tooff. When enabled, the Node sends stream and message data to wstore, allowing API Discovery to build the API inventory and display gRPC/WebSocket endpoints in the Wallarm Console UI. -
Fixed the stuffed credentials export to the Cloud
-
Improved GraphQL parser
-
Bug fixes and internal improvements
6.3.1 (2025-07-23)¶
- Fixed memory leak
6.3.0 (2025-07-08)¶
-
Added support for file upload restriction policy via mitigation controls
-
Added support for unrestricted resource consumption mitigation by API Abuse Prevention
-
Added support for the
postanalytics.wstore.config.serviceAddressparameter to customize the address and port for incoming wstore connections -
In rules, the separator used in xml_tag values that combine a URI, namespace, and tag name has been changed from
:to| -
Internal improvements
6.2.0 (2025-06-20)¶
-
Added support for mitigation control-based GraphQL API Protection
-
Optimized stream handling for gRPC traffic
-
Optimized stream handling for gRPC traffic
-
Added support for SSL/TLS and mTLS between the Filtering Node and the postanalytics module
-
Bump Alpine version to 3.22
-
Upgrade NGINX to version 1.28.0
-
Minor bug fixes
6.1.0 (2025-05-09)¶
-
Bugfix: Attacks originated from allowlisted sources are no longer shown in the Attacks section
-
wstore logs now include
"component": "wstore"for easier identification
6.0.1 (2025-04-22)¶
- Fixed the CVE-2024-56406, CVE-2025-31115 vulnerabilities
6.0.0 (2025-04-03)¶
- Initial release 6.0, see changelog
Helm chart for eBPF-based solution¶
0.23.0 (2026-02-28)¶
-
Updated the eBPF-based solution (beta) for API Discovery — building your API inventory based on real traffic without impacting production
-
Switched the processing component from NGINX-based node (
wallarm/node-nginx) to Native Node (wallarm/node-native-processing), addedconfig.connectorsection for its configuration -
Enabled metrics by default for processing and agent components
-
Renamed and restructured Helm chart parameters:
What changed Old value New value Aggregation in-memory storage parameter config.aggregation.tarantoolMemoryconfig.aggregation.wstoreMemoryProcess manager configuration section config.supervisordconfig.wcliResponder section config.responderRemoved Processing pod containers node,responder,supervisord,collectdnodeNative,wcliAggregation pod containers supervisord,tarantool,appStructure,antiBotwcli,wstore
NGINX-based Docker image¶
6.12.3 (2026-05-25)¶
-
Added BoringSSL compatibility — the Wallarm NGINX module can now run on BoringSSL-linked NGINX builds. JA4 TLS fingerprinting and encrypted upstream traffic to the postanalytics service are disabled when the build lacks the required symbols
-
Fixed the HEX parser producing false detections on very short alphanumeric inputs such as two-character values
-
Fixed HEX-encoded points in serialized requests causing parsing errors in the postanalytics service and API Discovery
-
Fixed API Discovery inferring the wrong content type for responses — the value is now read from request-level metadata instead of the response
Content-Typeheader -
Fixed gRPC and WebSocket responses being blocked on detected infoleaks
6.12.2 (2026-05-19)¶
- Pulled in NGINX security patches from the Alpine base image: CVE-2026-42945, CVE-2026-42946, CVE-2026-40460, CVE-2026-42934, and CVE-2026-40701.
6.12.1 (2026-05-12)¶
- Internal improvements
6.12.0 (2026-05-04)¶
-
Added support for MCP server discovery in API Discovery
-
Added support for MCP Sessions
-
Added MCP mitigation controls: ACL policy, request verification, and tool input schema enforcement
-
Added HEX encoding attack detection — the Node now decodes and analyzes HEX-encoded payloads, improving protection against obfuscation-based bypass techniques
-
Added per-tenant statistics and logging in multi-tenant deployments:
- The
wallarm_partner_client_uuiddirective now accepts an optional human-readable label - Two new NGINX variables (
$wallarm_partner_client_uuid,$wallarm_partner_client_label) are available for use in extended log formats - The
wallarm_statusendpoint now includes per-tenant traffic breakdown in both JSON and Prometheus output formats — per-application (wallarm_*_per_app_totalmetrics) and per-group (wallarm_*_per_group_totalmetrics) via thewallarm_status_groupdirective
- The
-
Added
?format=jsonand?format=prometheusquery parameter support to thewallarm_statusendpoint, allowing the output format to be overridden at request time -
Fixed API Specification Enforcement incorrectly reporting requests as "undefined endpoint" for OpenAPI specs that define a base path in the
serversblock -
Bumped Go version to 1.26.1
6.11.3 (2026-04-29)¶
-
Fixed intermittent errors in custom ruleset loading and GraphQL processing
-
Fixed NGINX worker crash (signal 11) when serving custom blocking pages configured via file path while response header modification rules were active
6.11.2 (2026-03-27)¶
-
Bump Alpine version to 3.23
-
Upgrade NGINX to version 1.28.3
6.11.1 (2026-03-25)¶
-
Added authentication flow detection in API Discovery — automatically identifies authentication methods used by each endpoint and highlights unauthenticated endpoints
-
Fixed empty response (
000status code) instead of custom block page whenngx_http_auth_request_moduleis used -
Fixed the GHSA-6g7g-w4f8-9c9x vulnerability
-
Bumped Go version to 1.26.1
6.10.3 (2026-03-16)¶
- Fixed a memory leak in the API Specification Enforcement component that caused steadily increasing memory consumption and eventual OOMKill pod restarts
6.10.2 (2026-03-10)¶
-
Added new traffic metrics to the
wallarm-statusstatistics service:bytes_blocked_in,bytes_blocked_out,bytes_blocked_by_acl_in, andbytes_blocked_by_acl_outThese counters track the volume of incoming and outgoing traffic in blocked requests, split by block reason (attack/overlimit/antibot vs. denylists). Available in JSON, Prometheus, and per-application split formats.
-
Fixed a shared memory allocation bug in the statistics service initialization that could lead to data corruption under high load
-
Fixed memory limit handling for wcli jobs
-
Fixed security vulnerabilities:
- CVE-2025-68121
- CVE-2026-25646
- CVE-2025-61726
6.10.1 (2026-02-18)¶
- Added support for circular references in OpenAPI specifications uploaded for API Specification Enforcement
6.10.0 (2026-02-09)¶
-
Added support for OpenAPI v3 specifications with non-string (for example, integer) YAML keys in API Specification Enforcement. This improves compatibility and prevents schema parsing failures
-
Fixed an issue where the Node sent too many requests in a single batch to wstore, causing submission failures
6.9.0 (2026-01-15)¶
-
Increased the frequency of session updates sent to the Wallarm Cloud. Sessions now appear in the UI faster, closer to real time
-
Improved memory usage monitoring and prevention of resource exhaustion
-
Fixed the CVE-2026-21441 vulnerability
6.8.1 (2025-12-24)¶
-
Fixed an issue where malformed fuzzing traffic could cause NGINX crashes, as observed in logs
-
Added API token masking in Node logs to prevent sensitive data exposure
6.8.0 (2025-12-23)¶
- Bug fixes:
- Fixed the issue where integers were not being masked when using the "Mask sensitive data" rule
- Fixed the issue where responses containing infoleak stamps were being blocked. Wallarm no longer blocks such responses, as doing so caused false detections and prevented rules from being edited
- Fixed the issue where the
wallarm_statusservice statistics contained the outdatedabnormalmetric, which was incorrectly increasing with each request. The metric and other outdated fields have been removed
6.7.3 (2025-12-11)¶
- Fixed an issue where large or overlapping denylisted IP ranges were not being blocked in Security Edge-hosted environments
6.7.1 (2025-11-17)¶
- Fixed
'error: no error'when processing gRPC/WebSocket response attacks
6.7.0 (2025-11-05)¶
-
Introduced JA4 fingerprinting in the NGINX node
JA4 fingerprints help detect threats and malicious clients based on TLS handshake characteristics. JA4 fingerprints are used as an additional factor when deciding to block a request.
The feature is disabled by default. To enable it, add the following NGINX directive inside the
httporserverblock: -
Introduced the
wallarm_fingerprint_ja4_rawandwallarm_fingerprint_ja4variables to configure extended logging when JA4 fingerprinting is enabled -
Improved Node initialization logs — added detailed information about component type, supported versions, error source, API endpoint, and Node UUID to simplify troubleshooting during the initialization stage
-
Fixed the CVE-2025-58188 vulnerability
-
Fixed the issue where the Node raised an error when a JWT token was sent in the
Authorization: Bearerheader -
Fixed invalid type error when editing automatically created rules for attacks detected in gRPC responses
6.6.1 (2025-10-16)¶
-
Introduced support for OpenAPI 3.1 in the API Specification Enforcement feature — you can now upload specifications in version 3.1 format to compare traffic against them, identify mismatches, and mitigate related security risks
-
Fixed the following vulnerabilities:
6.6.0 (2025-10-03)¶
-
Changed the default wstore binding to IPv4 (
tcp4), it now listens only on IPv4 instead of dual‑stackIf your configuration uses
localhostfor wstore, update it to127.0.0.1. -
Introduced protocol selection (tcp, tcp4, tcp6) via the
WALLARM_WSTORE__SERVICE__PROTOCOLenvironment variableThe default value is
"tcp4". -
Fixed an issue where response context parameters configured in API Sessions were not uploaded to the Wallarm Cloud
-
Introduced a new Prometheus metric
wallarm_wcli_job_export_lagto track the average export delay for each wcli job (e.g.,reqexp,blkexp,botexp) -
Fixed an issue where Docker container logs showed a false error about inability to connect to port 3313 when
upstream wallarm_wstorewas configured withlocalhostinstead of127.0.0.1False error example:
-
Introduced a new
$wallarm_modevariable for extended loggingThis variable returns the final filtration mode applied to a malicious request, taking into account both local settings and those from the Wallarm Cloud (e.g., rules and mitigation controls) with their prioritization.
-
Included an SBOM in the image by default, you can retrieve it using the following command:
-
Updated the wording on the Wallarm-branded block page, the page now looks as follows:
-
Fixed the following vulnerabilities:
6.5.1 (2025-09-09)¶
-
Added support for blocking attackers by API sessions
-
Exposed wcli Controller metrics endpoint for external monitoring
-
Relaxed content-type validation in API Specification Enforcement: requests with image MIME types (
image/png,image/jpeg,image/gif,image/webp,image/avif,image/heic,image/heif,image/bmp,image/tiff,image/svg+xml) are no longer rejected -
Bumped Go version to 1.24
-
Fixed the behavior of the
wallarm_wstore_throttle_modePrometheus metric, which previously did not return to the normal state (0) after throttling ended
6.4.1 (2025-08-07)¶
-
Added Prometheus metrics support for API Specification Enforcement service operation (based on the built-in API Firewall service):
- Enable with the environment variable
APIFW_METRICS_ENABLED=true - Default endpoint:
:9010/metrics - Expose the metrics port in your container (e.g., for the default state, use
-p 9010:9010) - Host and endpoint name configurable via variables
APIFW_METRICS_HOSTandAPIFW_METRICS_ENDPOINT_NAME
- Enable with the environment variable
6.4.0 (2025-07-31)¶
-
Introduced a new
wallarm_block_reasonvariable for extended loggingThis variable adds to the log an information on reason of request blocking (detected attack, part of bot activity, Denylist etc.)
-
Introduced the new
wallarm_export_streamsWallarm directive which controls whether the Node exports information about long-lived streaming connections to the internal postanalytics storage (wstore)By default,
wallarm_export_streamsis set tooff. When enabled, the Node sends stream and message data to wstore, allowing API Discovery to build the API inventory and display gRPC/WebSocket endpoints in the Wallarm Console UI. -
Fixed the stuffed credentials export to the Cloud
-
Improved GraphQL parser
-
Bug fixes and internal improvements
6.3.1 (2025-07-23)¶
- Fixed memory leak
6.3.0 (2025-07-08)¶
-
Added support for file upload restriction policy via mitigation controls
-
Added support for unrestricted resource consumption mitigation by API Abuse Prevention
-
In rules, the separator used in xml_tag values that combine a URI, namespace, and tag name has been changed from
:to| -
Internal improvements
6.2.0 (2025-06-20)¶
-
Added support for mitigation control-based GraphQL API Protection
-
Optimized stream handling for gRPC traffic
-
Optimized stream handling for gRPC traffic
-
Added the
streamsandmessagesparameters to the/wallarm-statusservice output to report the number of processed gRPC/WebSocket streams and messages -
Added support for SSL/TLS and mTLS between the NGINX-Wallarm module and the postanalytics module when they are installed separately
-
Fixed wstore ports binding: now bound to
127.0.0.1instead of0.0.0.0 -
Bump Alpine version to 3.22
-
Upgrade NGINX to version 1.28.0
-
Minor bug fixes
6.1.0 (2025-05-09)¶
-
Bugfix: Attacks originated from allowlisted sources are no longer shown in the Attacks section
-
wstore logs now include
"component": "wstore"for easier identification
6.0.1 (2025-04-22)¶
- Fixed the CVE-2024-56406, CVE-2025-31115 vulnerabilities
6.0.0 (2025-04-03)¶
- Initial release 6.0, see changelog
Amazon Machine Image (AMI)¶
6.12.3 (2026-05-25)¶
-
Added BoringSSL compatibility — the Wallarm NGINX module can now run on BoringSSL-linked NGINX builds. JA4 TLS fingerprinting and encrypted upstream traffic to the postanalytics service are disabled when the build lacks the required symbols
-
Fixed the HEX parser producing false detections on very short alphanumeric inputs such as two-character values
-
Fixed HEX-encoded points in serialized requests causing parsing errors in the postanalytics service and API Discovery
-
Fixed API Discovery inferring the wrong content type for responses — the value is now read from request-level metadata instead of the response
Content-Typeheader -
Fixed gRPC and WebSocket responses being blocked on detected infoleaks
6.12.2 (2026-05-19)¶
- Pulled in NGINX security patches from the Debian base image: CVE-2026-27651, CVE-2026-27654, CVE-2026-27784, CVE-2026-28753, CVE-2026-28755, CVE-2026-32647, CVE-2026-40701, CVE-2026-42934, CVE-2026-42945, and CVE-2026-42946.
6.12.1 (2026-05-12)¶
- Internal improvements
6.12.0 (2026-05-04)¶
-
Added support for MCP server discovery in API Discovery
-
Added support for MCP Sessions
-
Added MCP mitigation controls: ACL policy, request verification, and tool input schema enforcement
-
Added HEX encoding attack detection — the Node now decodes and analyzes HEX-encoded payloads, improving protection against obfuscation-based bypass techniques
-
Added per-tenant statistics and logging in multi-tenant deployments:
- The
wallarm_partner_client_uuiddirective now accepts an optional human-readable label - Two new NGINX variables (
$wallarm_partner_client_uuid,$wallarm_partner_client_label) are available for use in extended log formats - The
wallarm_statusendpoint now includes per-tenant traffic breakdown in both JSON and Prometheus output formats — per-application (wallarm_*_per_app_totalmetrics) and per-group (wallarm_*_per_group_totalmetrics) via thewallarm_status_groupdirective
- The
-
Added
?format=jsonand?format=prometheusquery parameter support to thewallarm_statusendpoint, allowing the output format to be overridden at request time -
Fixed API Specification Enforcement incorrectly reporting requests as "undefined endpoint" for OpenAPI specs that define a base path in the
serversblock -
Bumped Go version to 1.26.1
6.11.2 (2026-03-27)¶
- Internal improvements
6.11.1 (2026-03-25)¶
-
Added authentication flow detection in API Discovery — automatically identifies authentication methods used by each endpoint and highlights unauthenticated endpoints
-
Fixed empty response (
000status code) instead of custom block page whenngx_http_auth_request_moduleis used -
Fixed the GHSA-6g7g-w4f8-9c9x vulnerability
-
Bumped Go version to 1.26.1
6.10.3 (2026-03-16)¶
- Fixed a memory leak in the API Specification Enforcement component that caused steadily increasing memory consumption and eventual OOMKill pod restarts
6.10.2 (2026-03-10)¶
-
Added new traffic metrics to the
wallarm-statusstatistics service:bytes_blocked_in,bytes_blocked_out,bytes_blocked_by_acl_in, andbytes_blocked_by_acl_outThese counters track the volume of incoming and outgoing traffic in blocked requests, split by block reason (attack/overlimit/antibot vs. denylists). Available in JSON, Prometheus, and per-application split formats.
-
Fixed a shared memory allocation bug in the statistics service initialization that could lead to data corruption under high load
-
Fixed memory limit handling for wcli jobs
-
Fixed security vulnerabilities:
6.10.1 (2026-02-18)¶
- Added support for circular references in OpenAPI specifications uploaded for API Specification Enforcement
6.10.0 (2026-02-09)¶
-
Added support for OpenAPI v3 specifications with non-string (for example, integer) YAML keys in API Specification Enforcement. This improves compatibility and prevents schema parsing failures
-
Fixed an issue where the Node sent too many requests in a single batch to wstore, causing submission failures
6.9.0 (2026-01-15)¶
-
Increased the frequency of session updates sent to the Wallarm Cloud. Sessions now appear in the UI faster, closer to real time
-
Improved memory usage monitoring and prevention of resource exhaustion
-
Fixed the CVE-2026-21441 vulnerability
6.8.1 (2025-12-24)¶
-
Fixed an issue where malformed fuzzing traffic could cause NGINX crashes, as observed in logs
-
Added API token masking in Node logs to prevent sensitive data exposure
6.8.0 (2025-12-23)¶
- Bug fixes:
- Fixed the issue where integers were not being masked when using the "Mask sensitive data" rule
- Fixed the issue where responses containing infoleak stamps were being blocked. Wallarm no longer blocks such responses, as doing so caused false detections and prevented rules from being edited
- Fixed the issue where the
wallarm_statusservice statistics contained the outdatedabnormalmetric, which was incorrectly increasing with each request. The metric and other outdated fields have been removed
6.7.3 (2025-12-11)¶
- Fixed an issue where large or overlapping denylisted IP ranges were not being blocked in Security Edge-hosted environments
6.7.1 (2025-11-17)¶
-
Node installation now requires that no system user named
wallarmexists -
Introduced JA4 fingerprinting in the NGINX node
JA4 fingerprints help detect threats and malicious clients based on TLS handshake characteristics. JA4 fingerprints are used as an additional factor when deciding to block a request.
The feature is disabled by default. To enable it, add the following NGINX directive inside the
httporserverblock: -
Introduced the
wallarm_fingerprint_ja4_rawandwallarm_fingerprint_ja4variables to configure extended logging when JA4 fingerprinting is enabled -
Improved Node initialization logs — added detailed information about component type, supported versions, error source, API endpoint, and Node UUID to simplify troubleshooting during the initialization stage
-
Fixed the CVE-2025-58188 vulnerability
-
Fixed the issue where the Node raised an error when a JWT token was sent in the
Authorization: Bearerheader -
Fixed invalid type error when editing automatically created rules for attacks detected in gRPC responses
-
Fixed
'error: no error'when processing gRPC/WebSocket response attacks
6.6.1 (2025-10-16)¶
-
Introduced support for OpenAPI 3.1 in the API Specification Enforcement feature — you can now upload specifications in version 3.1 format to compare traffic against them, identify mismatches, and mitigate related security risks
-
Fixed the following vulnerabilities:
6.6.0 (2025-10-03)¶
-
Changed the default wstore binding to IPv4 (
tcp4), it now listens only on IPv4 instead of dual‑stackIf your configuration uses
localhostfor wstore, update it to127.0.0.1. -
Introduced protocol selection (tcp, tcp4, tcp6) using the
WALLARM_WSTORE__SERVICE__PROTOCOLenvironment variable, which can be set in/opt/wallarm/env.listThe default value is
"tcp4". -
Fixed an issue where response context parameters configured in API Sessions were not uploaded to the Wallarm Cloud
-
Introduced a new Prometheus metric
wallarm_wcli_job_export_lagto track the average export delay for each wcli job (e.g.,reqexp,blkexp,botexp) -
Introduced a new
$wallarm_modevariable for extended loggingThis variable returns the final filtration mode applied to a malicious request, taking into account both local settings and those from the Wallarm Cloud (e.g., rules and mitigation controls) with their prioritization.
-
Updated the wording on the Wallarm-branded block page, the page now looks as follows:
6.5.1 (2025-09-09)¶
-
Added support for blocking attackers by API sessions
-
Exposed wcli Controller metrics endpoint for external monitoring
-
Relaxed content-type validation in API Specification Enforcement: requests with image MIME types (
image/png,image/jpeg,image/gif,image/webp,image/avif,image/heic,image/heif,image/bmp,image/tiff,image/svg+xml) are no longer rejected -
Bumped Go version to 1.24
-
Fixed the behavior of the
wallarm_wstore_throttle_modePrometheus metric, which previously did not return to the normal state (0) after throttling ended
6.4.0 (2025-07-31)¶
-
Introduced a new
wallarm_block_reasonvariable for extended loggingThis variable adds to the log an information on reason of request blocking (detected attack, part of bot activity, Denylist etc.)
-
Introduced the new
wallarm_export_streamsWallarm directive which controls whether the Node exports information about long-lived streaming connections to the internal postanalytics storage (wstore)By default,
wallarm_export_streamsis set tooff. When enabled, the Node sends stream and message data to wstore, allowing API Discovery to build the API inventory and display gRPC/WebSocket endpoints in the Wallarm Console UI. -
Fixed the stuffed credentials export to the Cloud
-
Improved GraphQL parser
-
Bug fixes and internal improvements
6.3.1 (2025-07-23)¶
- Fixed memory leak
6.3.0 (2025-07-08)¶
-
Added support for file upload restriction policy via mitigation controls
-
Added support for unrestricted resource consumption mitigation by API Abuse Prevention
-
In rules, the separator used in xml_tag values that combine a URI, namespace, and tag name has been changed from
:to| -
Internal improvements
6.2.0 (2025-06-20)¶
-
Added support for mitigation control-based GraphQL API Protection
-
Optimized stream handling for gRPC traffic
-
Optimized stream handling for gRPC traffic
-
Added the
streamsandmessagesparameters to the/wallarm-statusservice output to report the number of processed gRPC/WebSocket streams and messages -
Added support for SSL/TLS and mTLS between the NGINX-Wallarm module and the postanalytics module when they are installed separately
-
Fixed wstore ports binding: now bound to
127.0.0.1instead of0.0.0.0 -
Minor bug fixes
6.1.0 (2025-05-09)¶
-
Bugfix: Attacks originated from allowlisted sources are no longer shown in the Attacks section
-
wstore logs now include
"component": "wstore"for easier identification
6.0.1 (2025-04-22)¶
- Fixed the CVE-2024-56406, CVE-2025-31115 vulnerabilities
6.0.0 (2025-04-03)¶
- Initial release 6.0, see changelog
Google Cloud Platform Image¶
wallarm-node-6-12-3-20260522-031313 (2026-05-25)¶
-
Added BoringSSL compatibility — the Wallarm NGINX module can now run on BoringSSL-linked NGINX builds. JA4 TLS fingerprinting and encrypted upstream traffic to the postanalytics service are disabled when the build lacks the required symbols
-
Fixed the HEX parser producing false detections on very short alphanumeric inputs such as two-character values
-
Fixed HEX-encoded points in serialized requests causing parsing errors in the postanalytics service and API Discovery
-
Fixed API Discovery inferring the wrong content type for responses — the value is now read from request-level metadata instead of the response
Content-Typeheader -
Fixed gRPC and WebSocket responses being blocked on detected infoleaks
wallarm-node-6-12-2-20260518-171044 (2026-05-19)¶
- Pulled in NGINX security patches from the Debian base image: CVE-2026-27651, CVE-2026-27654, CVE-2026-27784, CVE-2026-28753, CVE-2026-28755, CVE-2026-32647, CVE-2026-40701, CVE-2026-42934, CVE-2026-42945, and CVE-2026-42946.
wallarm-node-6-12-1-20260512-212132 (2026-05-12)¶
- Internal improvements
wallarm-node-6-12-0-20260501-220140 (2026-05-04)¶
-
Added support for MCP server discovery in API Discovery
-
Added support for MCP Sessions
-
Added MCP mitigation controls: ACL policy, request verification, and tool input schema enforcement
-
Added HEX encoding attack detection — the Node now decodes and analyzes HEX-encoded payloads, improving protection against obfuscation-based bypass techniques
-
Added per-tenant statistics and logging in multi-tenant deployments:
- The
wallarm_partner_client_uuiddirective now accepts an optional human-readable label - Two new NGINX variables (
$wallarm_partner_client_uuid,$wallarm_partner_client_label) are available for use in extended log formats - The
wallarm_statusendpoint now includes per-tenant traffic breakdown in both JSON and Prometheus output formats — per-application (wallarm_*_per_app_totalmetrics) and per-group (wallarm_*_per_group_totalmetrics) via thewallarm_status_groupdirective
- The
-
Added
?format=jsonand?format=prometheusquery parameter support to thewallarm_statusendpoint, allowing the output format to be overridden at request time -
Fixed API Specification Enforcement incorrectly reporting requests as "undefined endpoint" for OpenAPI specs that define a base path in the
serversblock -
Bumped Go version to 1.26.1
wallarm-node-6-11-3-20260422-125758 (2026-04-29)¶
-
Fixed intermittent errors in custom ruleset loading and GraphQL processing
-
Fixed NGINX worker crash (signal 11) when serving custom blocking pages configured via file path while response header modification rules were active
wallarm-node-6-11-2-20260327-122303 (2026-03-27)¶
- Internal improvements
wallarm-node-6-11-1-20260325-092834 (2026-03-25)¶
-
Added authentication flow detection in API Discovery — automatically identifies authentication methods used by each endpoint and highlights unauthenticated endpoints
-
Fixed empty response (
000status code) instead of custom block page whenngx_http_auth_request_moduleis used -
Fixed the GHSA-6g7g-w4f8-9c9x vulnerability
-
Bumped Go version to 1.26.1
wallarm-node-6-10-3-20260312-143020 (2026-03-16)¶
- Fixed a memory leak in the API Specification Enforcement component that caused steadily increasing memory consumption and eventual OOMKill pod restarts
wallarm-node-6-10-2-20260310-115237 (2026-03-10)¶
-
Added new traffic metrics to the
wallarm-statusstatistics service:bytes_blocked_in,bytes_blocked_out,bytes_blocked_by_acl_in, andbytes_blocked_by_acl_outThese counters track the volume of incoming and outgoing traffic in blocked requests, split by block reason (attack/overlimit/antibot vs. denylists). Available in JSON, Prometheus, and per-application split formats.
-
Fixed a shared memory allocation bug in the statistics service initialization that could lead to data corruption under high load
-
Fixed memory limit handling for wcli jobs
-
Fixed security vulnerabilities:
wallarm-node-6-10-1-20260218-104823 (2026-02-18)¶
- Added support for circular references in OpenAPI specifications uploaded for API Specification Enforcement
wallarm-node-6-10-0-20260206-084755 (2026-02-09)¶
-
Added support for OpenAPI v3 specifications with non-string (for example, integer) YAML keys in API Specification Enforcement. This improves compatibility and prevents schema parsing failures
-
Fixed an issue where the Node sent too many requests in a single batch to wstore, causing submission failures
wallarm-node-6-9-0-20260113-150813 (2026-01-15)¶
-
Increased the frequency of session updates sent to the Wallarm Cloud. Sessions now appear in the UI faster, closer to real time
-
Improved memory usage monitoring and prevention of resource exhaustion
-
Fixed the CVE-2026-21441 vulnerability
wallarm-node-6-8-1-20251224-110807 (2025-12-24)¶
-
Fixed an issue where malformed fuzzing traffic could cause NGINX crashes, as observed in logs
-
Added API token masking in Node logs to prevent sensitive data exposure
wallarm-node-6-8-0-20251219-144249 (2025-12-23)¶
- Bug fixes:
- Fixed the issue where integers were not being masked when using the "Mask sensitive data" rule
- Fixed the issue where responses containing infoleak stamps were being blocked. Wallarm no longer blocks such responses, as doing so caused false detections and prevented rules from being edited
- Fixed the issue where the
wallarm_statusservice statistics contained the outdatedabnormalmetric, which was incorrectly increasing with each request. The metric and other outdated fields have been removed
wallarm-node-6-7-3-20251211-112314 (2025-12-11)¶
- Fixed an issue where large or overlapping denylisted IP ranges were not being blocked in Security Edge-hosted environments
wallarm-node-6-7-1-20251114-111054 (2025-11-17)¶
-
Node installation now requires that no system user named
wallarmexists -
Introduced JA4 fingerprinting in the NGINX node
JA4 fingerprints help detect threats and malicious clients based on TLS handshake characteristics. JA4 fingerprints are used as an additional factor when deciding to block a request.
The feature is disabled by default. To enable it, add the following NGINX directive inside the
httporserverblock: -
Introduced the
wallarm_fingerprint_ja4_rawandwallarm_fingerprint_ja4variables to configure extended logging when JA4 fingerprinting is enabled -
Improved Node initialization logs — added detailed information about component type, supported versions, error source, API endpoint, and Node UUID to simplify troubleshooting during the initialization stage
-
Fixed the CVE-2025-58188 vulnerability
-
Fixed the issue where the Node raised an error when a JWT token was sent in the
Authorization: Bearerheader -
Fixed invalid type error when editing automatically created rules for attacks detected in gRPC responses
-
Fixed
'error: no error'when processing gRPC/WebSocket response attacks
wallarm-node-6-6-1-20251015-165327 (2025-10-16)¶
-
Introduced support for OpenAPI 3.1 in the API Specification Enforcement feature — you can now upload specifications in version 3.1 format to compare traffic against them, identify mismatches, and mitigate related security risks
-
Fixed the following vulnerabilities:
wallarm-node-6-6-0-20251005-044509 (2025-10-03)¶
-
Changed the default wstore binding to IPv4 (
tcp4), it now listens only on IPv4 instead of dual‑stackIf your configuration uses
localhostfor wstore, update it to127.0.0.1. -
Introduced protocol selection (tcp, tcp4, tcp6) using the
WALLARM_WSTORE__SERVICE__PROTOCOLenvironment variable, which can be set in/opt/wallarm/env.listThe default value is
"tcp4". -
Fixed an issue where response context parameters configured in API Sessions were not uploaded to the Wallarm Cloud
-
Introduced a new Prometheus metric
wallarm_wcli_job_export_lagto track the average export delay for each wcli job (e.g.,reqexp,blkexp,botexp) -
Introduced a new
$wallarm_modevariable for extended loggingThis variable returns the final filtration mode applied to a malicious request, taking into account both local settings and those from the Wallarm Cloud (e.g., rules and mitigation controls) with their prioritization.
-
Updated the wording on the Wallarm-branded block page, the page now looks as follows:
wallarm-node-6-5-1-20250908-174655 (2025-09-09)¶
-
Added support for blocking attackers by API sessions
-
Relaxed content-type validation in API Specification Enforcement: requests with image MIME types (
image/png,image/jpeg,image/gif,image/webp,image/avif,image/heic,image/heif,image/bmp,image/tiff,image/svg+xml) are no longer rejected -
Bumped Go version to 1.24
-
Fixed the behavior of the
wallarm_wstore_throttle_modePrometheus metric, which previously did not return to the normal state (0) after throttling ended
wallarm-node-6-4-0-20250730-083353 (2025-07-31)¶
-
Introduced the new
wallarm_export_streamsWallarm directive which controls whether the Node exports information about long-lived streaming connections to the internal postanalytics storage (wstore)By default,
wallarm_export_streamsis set tooff. When enabled, the Node sends stream and message data to wstore, allowing API Discovery to build the API inventory and display gRPC/WebSocket endpoints in the Wallarm Console UI. -
Fixed the stuffed credentials export to the Cloud
-
Improved GraphQL parser
-
Bug fixes and internal improvements
wallarm-node-6-3-1-20250721-082413 (2025-07-23)¶
- Fixed memory leak
wallarm-node-6-3-0-20250708-175541 (2025-07-08)¶
-
In rules, the separator used in xml_tag values that combine a URI, namespace, and tag name has been changed from
:to| -
Internal improvements
wallarm-node-6-2-0-20250618-150224 (2025-06-20)¶
-
Optimized stream handling for gRPC traffic
-
Added the
streamsandmessagesparameters to the/wallarm-statusservice output to report the number of processed gRPC/WebSocket streams and messages -
Added support for SSL/TLS and mTLS between the NGINX-Wallarm module and the postanalytics module when they are installed separately
-
Fixed wstore ports binding: now bound to
127.0.0.1instead of0.0.0.0 -
Minor bug fixes
wallarm-node-6-1-0-20250508-144827 (2025-05-09)¶
-
Bugfix: Attacks originated from allowlisted sources are no longer shown in the Attacks section
-
wstore logs now include
"component": "wstore"for easier identification
wallarm-node-6-0-1-20250422-104749 (2025-04-22)¶
- Fixed the CVE-2024-56406, CVE-2025-31115 vulnerabilities
wallarm-node-6-0-0-20250403-102125 (2025-04-03)¶
- Initial release 6.0, see changelog