Upgrading the Docker NGINX-based image¶
These instructions describe the steps to upgrade the running Docker NGINX-based image to the latest version 6.x.
Using credentials of already existing Wallarm node
We do not recommend using the already existing Wallarm node of the previous version. Please follow these instructions to create a new filtering node of the version 6.x and deploy it as the Docker container.
To upgrade the end‑of‑life node (3.6 or lower), please use the different instructions.
Requirements¶
-
Docker installed on your host system
-
Access to
https://hub.docker.com/r/wallarm/nodeto download the Docker image. Please ensure the access is not blocked by a firewall -
Access to the account with the Administrator role in Wallarm Console in the US Cloud or EU Cloud, or ME Cloud
-
Access to
https://us1.api.wallarm.comif working with US Wallarm Cloud or tohttps://api.wallarm.comif working with EU Wallarm Cloud, tohttps://me1.api.wallarm.comif working with ME Wallarm Cloud. Please ensure the access is not blocked by a firewall -
Access to the IP addresses and their corresponding hostnames (if any) listed below. This is needed for downloading updates to attack detection rules and API specifications, as well as retrieving precise IPs for your allowlisted, denylisted, or graylisted countries, regions, or data centers
Step 1: Download the updated filtering node image¶
Step 2: Stop the running container¶
Step 3: Run the container using the new image¶
-
If upgrading from version 5.x or earlier, please note the following important changes:
- If you previously configured the postanalytics memory via the
TARANTOOL_MEMORY_GBenvironment variable, rename it toSLAB_ALLOC_ARENA. -
If you are running the Docker container with mounted custom NGINX configuration files:
-
The
includepaths in/etc/nginx/nginx.confhave changed to align with Alpine Linux directory conventions: -
In
/etc/nginx/conf.d/wallarm-status.conf, the default value of theallowdirective (used to define permitted IP addresses) has changed: -
The path for mounting virtual host configuration files has changed from
/etc/nginx/sites-enabled/defaultto/etc/nginx/http.d.
-
- If you previously configured the postanalytics memory via the
-
Proceed to Wallarm Console → Settings → API Tokens and generate a token with the Node deployment/Deployment usage type.
-
Copy the generated token.
-
Run the container using the new image and apply the updated configuration.
There are two options for running the container using the updated image:
Step 4: Test the filtering node operation¶
-
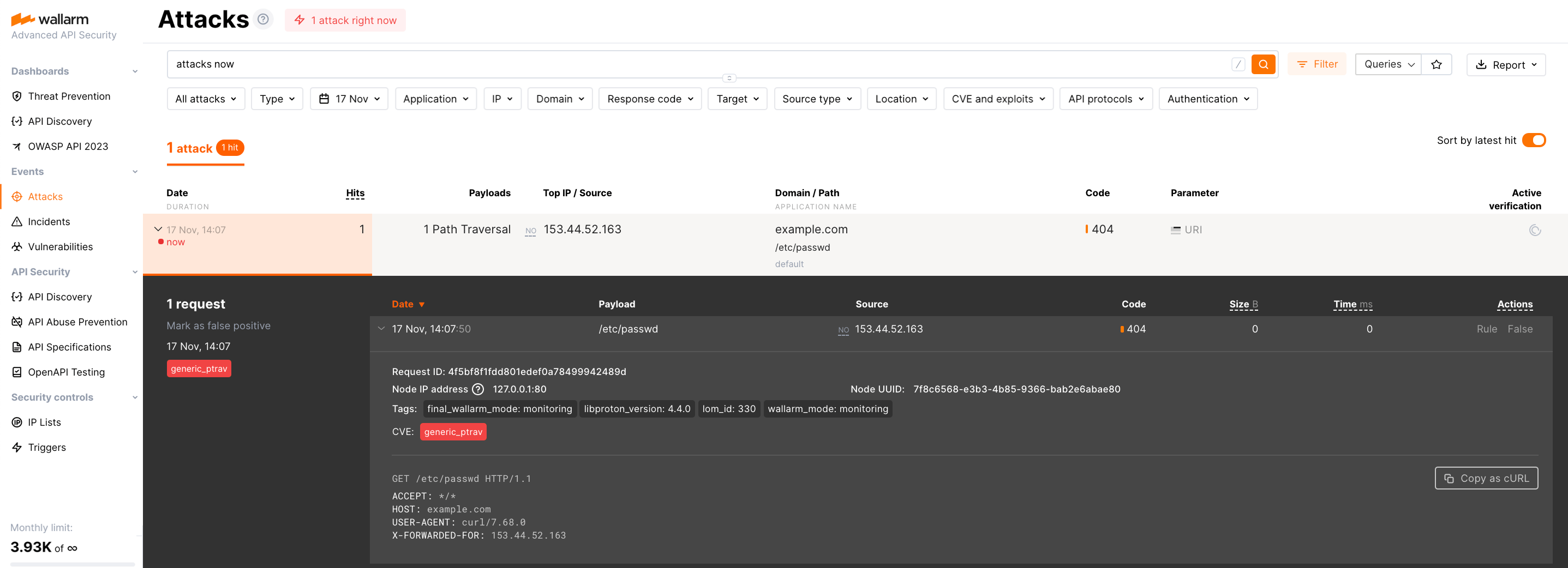
Send the request with test Path Traversal attack to a protected resource address:
If traffic is configured to be proxied to
example.com, include the-H "Host: example.com"header in the request. -
Open Wallarm Console → Attacks section in the US Cloud or EU Cloud, or ME Cloud and make sure the attack is displayed in the list.
-
Optionally, test other aspects of the node functioning.
Step 5: Delete the filtering node of the previous version¶
If the deployed image of the version 6.x operates correctly, you can delete the filtering node of the previous version in Wallarm Console → Nodes.