Configuration of Vulnerability Detection Process¶
FAST detects vulnerabilities using the following options:
-
Built-in FAST extensions
-
Custom extensions
To use custom extensions, please connect them to the FAST node.
You can control the way of detecting vulnerabilities in the application in the following ways:
-
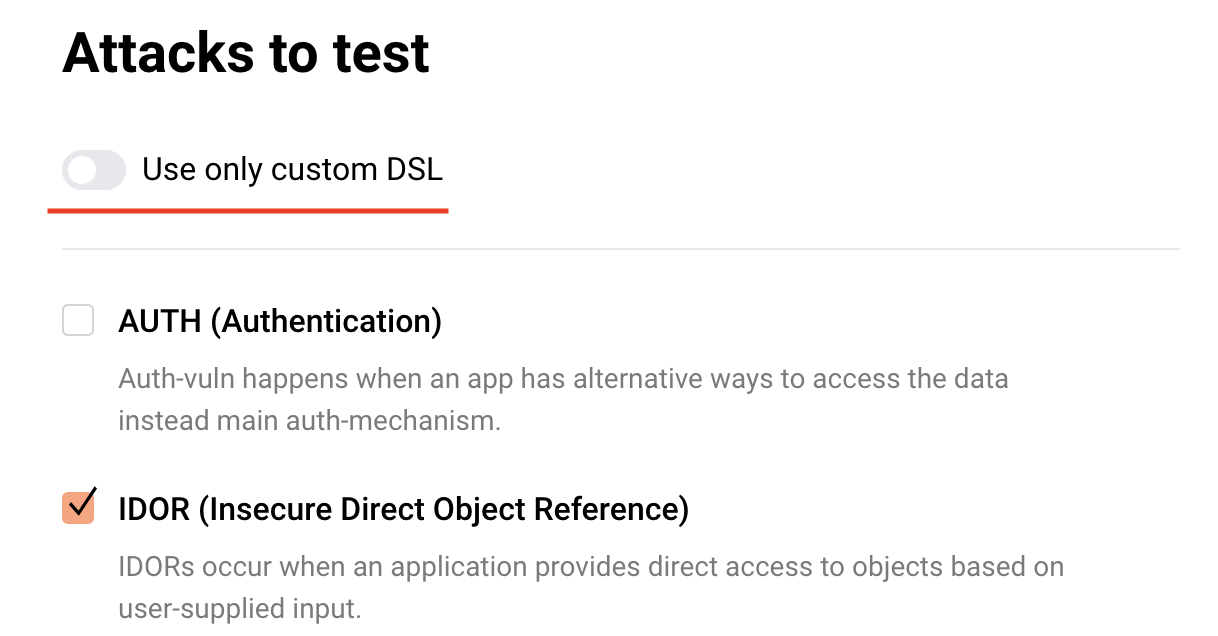
If you want to perform tests using the built-in FAST extension, then tick the vulnerability checkboxes you want to run tests on.
-
If you want to perform tests using only custom extensions excluding the built-in FAST extensions, then untick all the checkboxes or activate the Use only custom DSL switch and select vulnerabilities from the list.
Please note that if the Use only custom DSL switch is activated, then the built-in FAST extensions and FAST fuzzer will be disabled. If the FAST fuzzer is enabled, then the Use only custom DSL switch will become inactive again.
Basic vulnerabilities
When creating a policy, the most typical vulnerabilities that can be detected in applications are selected by default:
- path traversal (PTRAV),
- remote code execution (RCE),
- SQL injection (SQLi),
- cross-site scripting (XSS),
- vulnerability to attack on XML external entity (XXE).
If you use custom policies, you can disable testing the application for a specific vulnerability by unticking the corresponding checkbox at any moment.