Logstash¶
Logstash هو أداة مفتوحة المصدر لمعالجة البيانات وإدارة السجلات طورتها Elastic. يمكنك ضبط Wallarm لإرسال إشعارات بالأحداث المكتشفة إلى Logstash.
تنسيق الإشعار¶
Wallarm يرسل الإشعارات إلى Logstash عبر الويب هوك بتنسيق JSON. يعتمد مجموعة الكائنات JSON على الحدث الذي يشعر عنه Wallarm.
مثال على إشعار الضربة الجديدة المكتشفة:
[
{
"summary": "[Wallarm] New hit detected",
"details": {
"client_name": "TestCompany",
"cloud": "EU",
"notification_type": "new_hits",
"hit": {
"domain": "www.example.com",
"heur_distance": 0.01111,
"method": "POST",
"parameter": "SOME_value",
"path": "/news/some_path",
"payloads": [
"say ni"
],
"point": [
"post"
],
"probability": 0.01,
"remote_country": "PL",
"remote_port": 0,
"remote_addr4": "8.8.8.8",
"remote_addr6": "",
"tor": "none",
"request_time": 1603834606,
"create_time": 1603834608,
"response_len": 14,
"response_status": 200,
"response_time": 5,
"stamps": [
1111
],
"regex": [],
"stamps_hash": -22222,
"regex_hash": -33333,
"type": "sqli",
"block_status": "monitored",
"id": [
"hits_production_999_202010_v_1",
"c2dd33831a13be0d_AC9"
],
"object_type": "hit",
"anomaly": 0
}
}
}
]
المتطلبات¶
يجب أن تلبي تكوينات Logstash المتطلبات التالية:
-
قبول طلبات POST أو PUT
-
قبول طلبات HTTPS
-
امتلاك URL عام
مثال على تكوين Logstash:
يمكنك العثور على المزيد من التفاصيل في الوثائق الرسمية لـ Logstash.
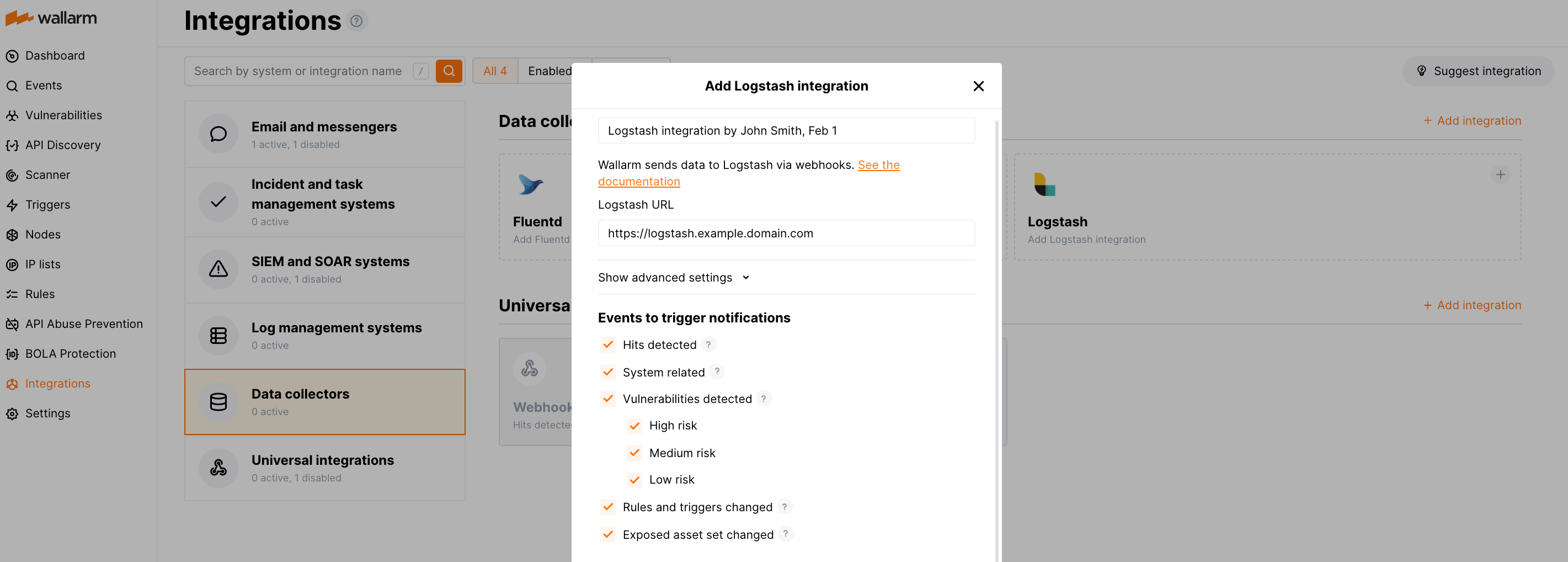
إعداد الاندماج¶
-
انتقل إلى إعداد اندماج Logstash في Wallarm Console → Integrations → Logstash.
-
أدخل اسم الاندماج.
-
حدد URL Logstash المستهدف (Webhook URL).
-
إذا لزم الأمر، قم بتهيئة الإعدادات المتقدمة:
- Request method:
POSTorPUT. By default, POST requests are sent. - Request header and its value if the server requires a non-standard header to execute the request. The number of headers is not limited.
- CA certificate: certificate of CA that signed a server certificate. If CA is publicly trusted, this field is optional. If a server certificate is self-signed, this field is required and must contain a certificate of your own CA that signed a server certificate.
- Verify TLS certificate: this setting allows to disable verification of the specified server certificate. By default, Wallarm verifies whether a server certificate is signed by a publicly trusted CA. We do not recommend disabling the verification of production server certificates. If your server uses a self-signed TLS certificate, you can add a self-signed CA certificate to allow sending requests to this server.
- Request timeout, in seconds: if the server does not respond to the request within the specified time, the request fails. By default: 15 seconds.
- Connection timeout, in seconds: if the connection to the server cannot be established during the specified time, the request fails. By default: 20 seconds.
- Wallarm data format: either a JSON Array (default) or a New Line Delimited JSON (NDJSON).
- Request method:
-
اختر أنواع الأحداث لتشغيل الإشعارات.
التفاصيل حول الأحداث المتاحة:
-
Hits detected except for:
- Experimental hits detected based on the custom regular expression. Non-experimental hits trigger notifications.
- Hits not saved in the sample.
Optionally include the
headersobject with hit headers in hit logs. If disabled, headers are not included in the logs. -
System related:
- User changes (newly created, deleted, role change)
- Integration changes (disabled, deleted)
- Application changes (newly created, deleted, name change)
- Errors during regular update of specifications used for rogue API detection or API specification enforcement
- Vulnerabilities detected, all by default or only for the selected risk level(s) - high, medium or low.
- Rules and triggers changed (creating, updating, or deleting the rule or trigger)
- On an hourly basis, you can get a notification with the number of requests processed during the previous hour
-
-
انقر اختبر الاندماج للتحقق من صحة التكوين، توافر Wallarm Cloud، وتنسيق الإشعار.
سجل Logstash التجريبي:
[ { summary:"[Test message] [Test partner(US)] New vulnerability detected", description:"Notification type: vuln New vulnerability was detected in your system. ID: Title: Test Domain: example.com Path: Method: Discovered by: Parameter: Type: Info Threat: Medium More details: https://us1.my.wallarm.com/object/555 Client: TestCompany Cloud: US ", details:{ client_name:"TestCompany", cloud:"US", notification_type:"vuln", vuln_link:"https://us1.my.wallarm.com/object/555", vuln:{ domain:"example.com", id:null, method:null, parameter:null, path:null, title:"Test", discovered_by:null, threat:"Medium", type:"Info" } } } ] -
انقر أضف اندماج.
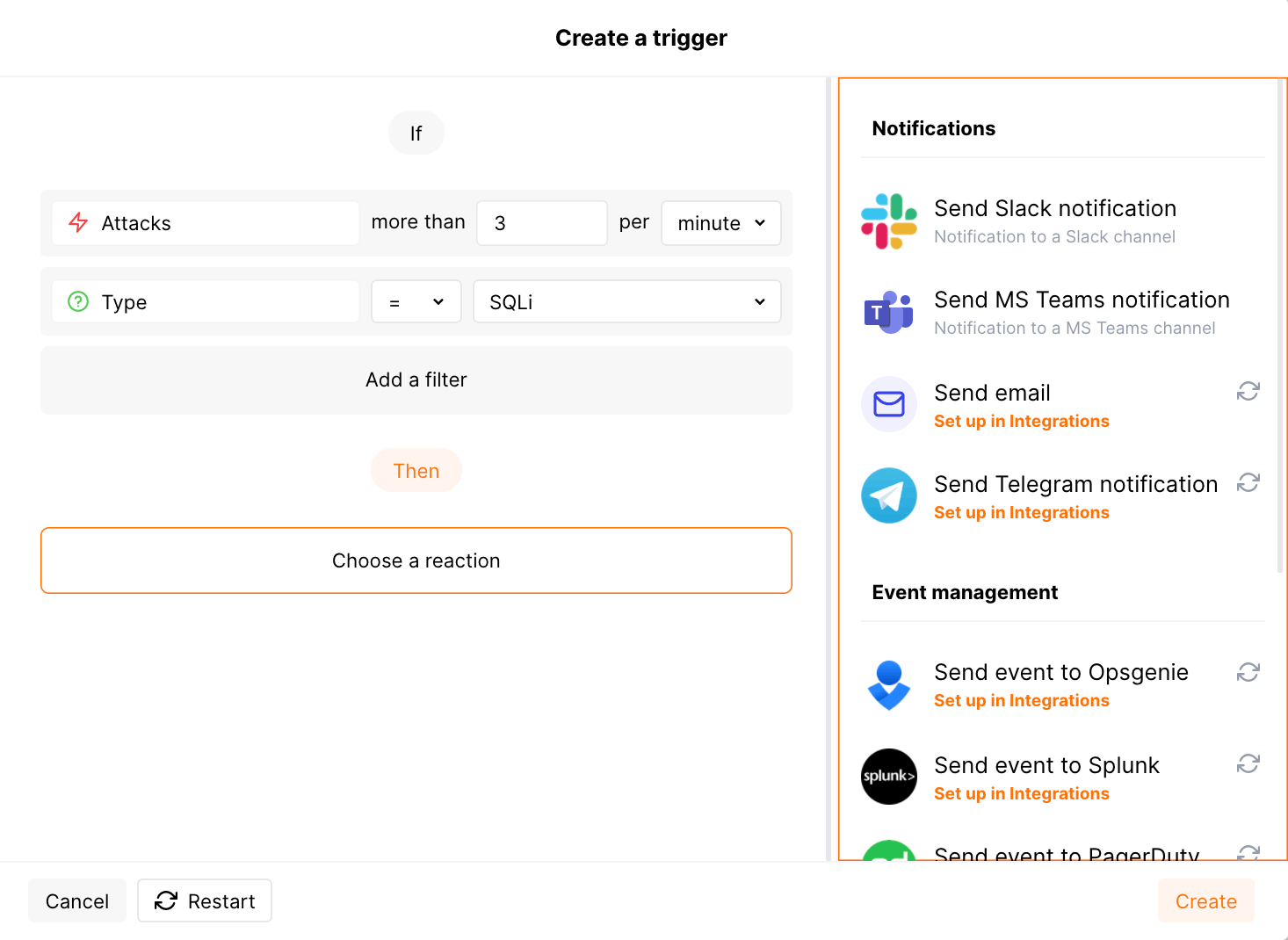
إعداد تنبيهات إضافية¶
Besides the notifications you have already set up through the integration card, Wallarm triggers allow you to select additional events for notifications:
-
Number of attacks, hits or incidents per time interval (day, hour, etc.) exceeds the set number
What is not counted
- For attacks:
- The experimental attacks based on the custom regular expressions.
- For hits:
- The experimental hits based on the custom regular expressions.
- Hits not saved in the sample.
- For attacks:
-
Changes in API took place
-
IP address was denylisted
-
New rogue API (shadow, zombie) was detected
-
New user was added to the company account
For condition detailing, you can add one or more filters. As soon, as condition and filters are set, select the integration through which the selected alert should be sent. You can select several integrations simultaneously.
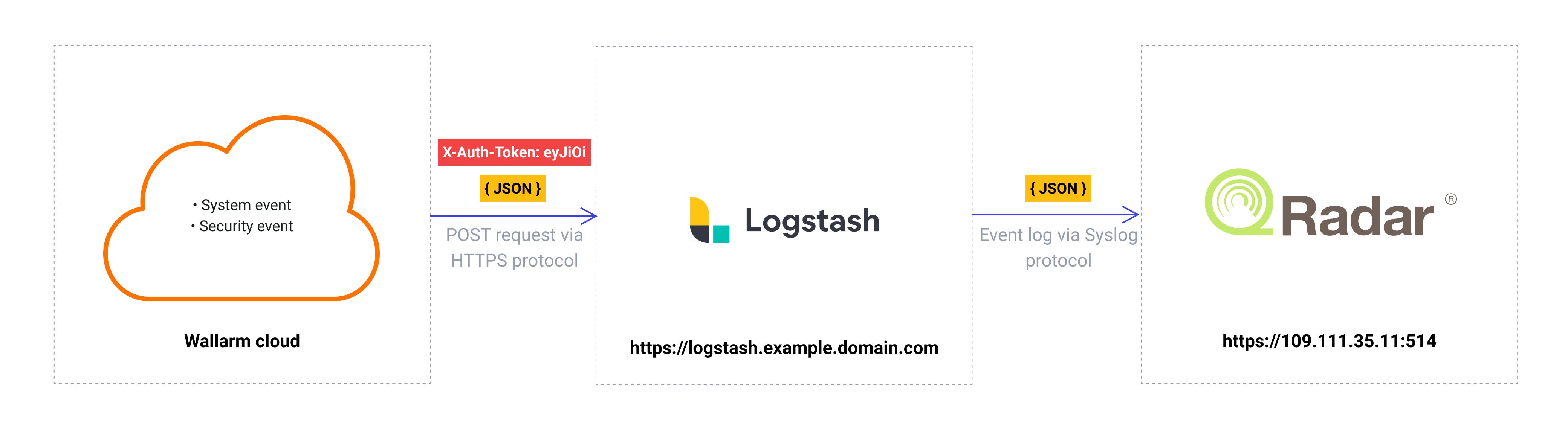
استخدام Logstash كمجمع بيانات وسيط¶
The most common logging scheme in complex systems consists of the following components:
-
Data collector: accepts logs from several sources and forwards logs to the SIEM system
-
SIEM system or log management systems: used to analyze logs and monitor the system status
على سبيل المثال:
لتسجيل أحداث Wallarm باستخدام هذه الخطة:
-
قم بتكوين مجمع البيانات لقراءة الويب هوك الواردة ولإعادة توجيه السجلات إلى النظام التالي. Wallarm يرسل الأحداث إلى مجمعي البيانات عبر الويب هوك.
-
قم بتكوين نظام إدارة المعلومات الأمنية لاستقبال وقراءة السجلات من مجمع البيانات.
-
قم بتكوين Wallarm لإرسال السجلات إلى مجمع البيانات.
يمكن لـ Wallarm إرسال السجلات إلى أي مجمع بيانات عبر الويب هوك.
للاندماج مع Fluentd أو Logstash، يمكنك استخدام بطاقات الاندماج المقابلة في واجهة مستخدم Wallarm Console.
للاندماج مع مجمعي بيانات آخرين، يمكنك استخدام بطاقة الاندماج عبر الويب هوك في واجهة مستخدم Wallarm Console.
وصفنا بعض الأمثلة على كيفية تكوين الاندماج مع مجمعي البيانات الشهيرة الموجهة لأنظمة إدارة المعلومات الأمنية:
-
كما يدعم Wallarm الاندماج الأصلي مع Datadog عبر واجهة برمجة تطبيقات Datadog. الاندماج الأصلي لا يتطلب استخدام مجمع بيانات وسيط.
تعطيل وحذف اندماج¶
You can delete or temporarily disable the integration. While deleting stops sending notificatioins and completely deletes all configuration, disabling just stops sending notifications which you can at any moment re-enable with the same settings.
If for the integration the System related events are selected to trigger notifications, Wallarm will notify about both of these actions.