التوظيف باستخدام الأداة All-in-One¶
توفر هذه التعليمات الخطوات التي توضح كيفية تثبيت Wallarm كوحدة نمطية ديناميكية OOB باستخدام أداة التثبيت All-in-One المصممة لتبسيط وتوحيد عملية تثبيت وحدة Wallarm النمطية التي تعمل كوحدة لـ NGINX في مختلف البيئات. تقوم هذه الأداة بتحديد نظام التشغيل وإصدارات NGINX تلقائياً، ثم تثبت جميع الاعتمادات اللازمة.
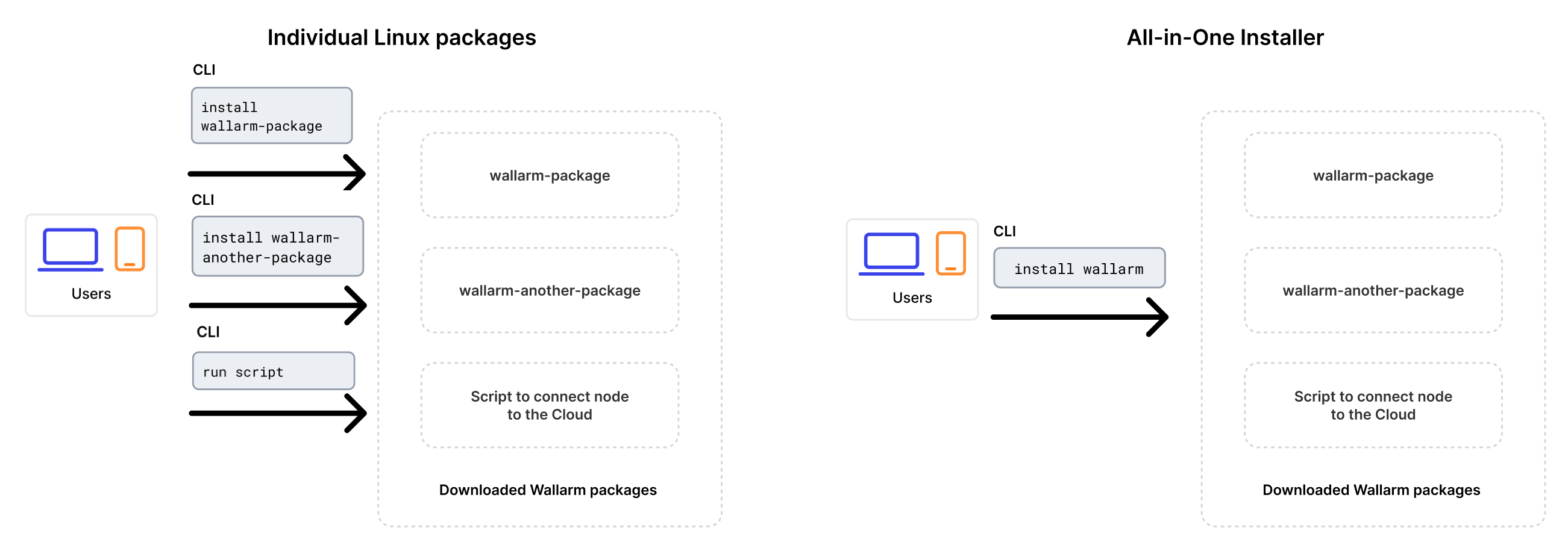
بالمقارنة بالحزم الفردية لنظام التشغيل Linux التي توفرها Wallarm لـ NGINX، وNGINX Plus، ونسخة NGINX الموزعة مسبقًا، تبسط أداة التثبيت All-in-One العملية من خلال القيام تلقائياً بالإجراءات التالية:
-
التحقق من نظام التشغيل وإصدار NGINX الخاص بك.
-
إضافة مستودعات Wallarm لنظام التشغيل وإصدار NGINX المكتشف.
-
تثبيت حزم Wallarm من هذه المستودعات.
-
التوصيل بوحدة Wallarm المثبتة مع NGINX الخاص بك.
-
توصيل العقدة التصفية بـ Wallarm Cloud باستخدام الرمز المميز المقدم.
سيناريوهات الاستخدام¶
Among all supported Wallarm deployment options, this solution is the recommended one for the following use cases:
-
Your infrastructure is based on bare metal or virtual machines without using container-based methods. Typically, these setups are managed with Infrastructure as Code (IaC) tools like Ansible or SaltStack.
-
Your services are built around NGINX. Wallarm can extend its functionalities using the all-in-one installer.
المتطلبات¶
-
Access to the account with the Administrator role in Wallarm Console for the US Cloud or EU Cloud.
-
Supported OS:
- Debian 10, 11 and 12.x
- Ubuntu LTS 18.04, 20.04, 22.04
- CentOS 7, 8 Stream, 9 Stream
- Alma/Rocky Linux 9
- RHEL 8.x
- Oracle Linux 8.x
- Oracle Linux 9.x
- Redox
- SuSe Linux
- Others (the list is constantly widening, contact Wallarm support team to check if your OS is in the list)
-
Access to
https://meganode.wallarm.comto download all-in-one Wallarm installer. Ensure the access is not blocked by a firewall. -
Access to
https://us1.api.wallarm.comfor working with US Wallarm Cloud or tohttps://api.wallarm.comfor working with EU Wallarm Cloud. If access can be configured only via the proxy server, then use the instructions. -
Access to the IP addresses and their corresponding hostnames (if any) listed below. This is needed for downloading updates to attack detection rules, as well as retrieving precise IPs for your allowlisted, denylisted, or graylisted countries, regions, or data centers
-
Executing all commands as a superuser (e.g.
root).
الخطوة 1: تثبيت NGINX والاعتمادات اللازمة¶
Install the latest NGINX version of:
-
NGINX
stable(the latest supported version is v1.28.1) - see how to install it in the NGINX documentation. -
NGINX Mainline (the latest supported version is v1.27.5) - see how to install it in the NGINX documentation.
-
NGINX Plus (the latest supported version is NGINX Plus R33) - see how to install it in the NGINX documentation.
-
Distribution-Provided NGINX - to install, use the following commands:
الخطوة 2: استعد رمز Wallarm المميز¶
To install node, you will need a Wallarm token of the appropriate type. To prepare a token:
الخطوة 3: تحميل المثبت All-in-One من Wallarm¶
Wallarm suggests all-in-one installations for the following processors:
-
x86_64
-
ARM64
To download all-in-one Wallarm installation script, execute the command:
الخطوة 4: تشغيل المثبت All-in-One من Wallarm¶
-
Run downloaded script:
# If using the x86_64 version: sudo env WALLARM_LABELS='group=<GROUP>' sh wallarm-6.9.0.x86_64-glibc.sh # If using the ARM64 version: sudo env WALLARM_LABELS='group=<GROUP>' sh wallarm-6.9.0.aarch64-glibc.shThe
WALLARM_LABELSvariable sets group into which the node will be added (used for logical grouping of nodes in the Wallarm Console UI). -
Enter Wallarm token.
أوامر الخطوات اللاحقة هي نفسها للتثبيتات x86_64 و ARM64.
الخطوة 5: تمكين عقدة Wallarm لتحليل الحركة¶
By default, the deployed Wallarm node does not analyze incoming traffic.
Perform the following configuration in the NGINX configuration file on the machine with the installed node to configure Wallarm to process the traffic mirror:
-
For the Wallarm node to accept mirrored traffic, set the following configuration in the
serverNGINX block:wallarm_force server_addr $http_x_server_addr; wallarm_force server_port $http_x_server_port; # Change 222.222.222.22 to the address of the mirroring server set_real_ip_from 222.222.222.22; real_ip_header X-Forwarded-For; real_ip_recursive on; wallarm_force response_status 0; wallarm_force response_time 0; wallarm_force response_size 0;- The
set_real_ip_fromandreal_ip_headerdirectives are required to have Wallarm Console display the IP addresses of the attackers. - The
wallarm_force_response_*directives are required to disable analysis of all requests except for copies received from the mirrored traffic.
- The
-
For the Wallarm node to analyze the mirrored traffic, set the
wallarm_modedirective tomonitoring:Since malicious requests cannot be blocked, the only mode Wallarm accepts is monitoring. For in-line deployment, there are also safe blocking and blocking modes but even if you set the
wallarm_modedirective to a value different from monitoring, the node continues to monitor traffic and only record malicious traffic (aside from the mode set to off). -
If present, remove the
try_filesdirective from the NGINX locations to ensure traffic is directed to Wallarm without local file interference:
الخطوة 6: إعادة تشغيل NGINX¶
Restart NGINX using the following command:
الخطوة 7: تكوين إرسال الحركة إلى عقدة Wallarm¶
Configure your environment to mirror incoming traffic to an instance with the Wallarm node you are deploying. For configuration details, we recommend to refer to documentation on the solution you are going to use to produce the traffic mirror (web server, proxy server, etc.).
Inside the link, you will find the example configuration for NGINX, Traefik, Envoy.
الخطوة 8: تجربة عملية عقدة Wallarm¶
-
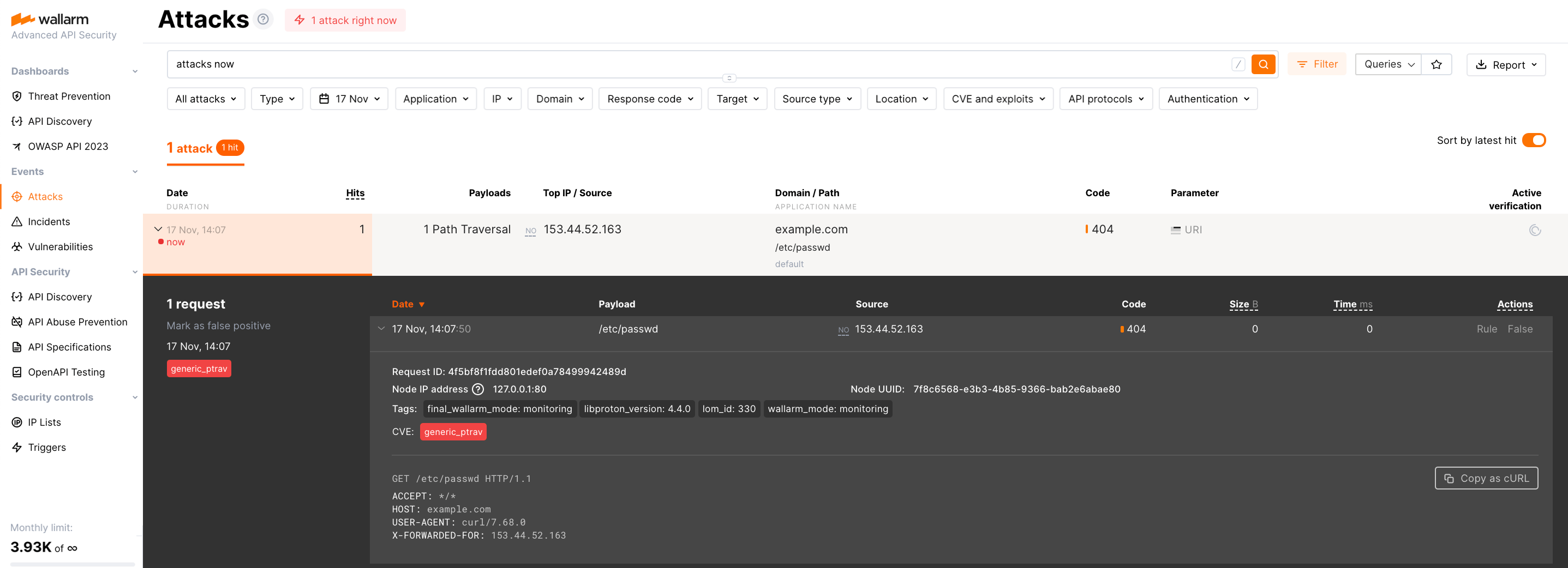
Send the request with test Path Traversal attack to a protected resource address:
If traffic is configured to be proxied to
example.com, include the-H "Host: example.com"header in the request. -
Open Wallarm Console → Attacks section in the US Cloud or EU Cloud and make sure the attack is displayed in the list.
-
Optionally, test other aspects of the node functioning.
الخطوة 9: ضبط الحل المنصوب بشكل دقيق¶
تم تثبيت الوحدة النمطية الديناميكية لـ Wallarm مع الإعدادات الافتراضية. قد تحتاج العقدة التصفية إلى بعض التكوينات الإضافية بعد النشر.
يتم تعريف إعدادات Wallarm باستخدام التوجيهات NGINX أو واجهة المستخدم الرسومية لـ Wallarm Console. يجب تعيين التوجيهات في الملفات التالية على الجهاز التي تحتوي على العقدة Wallarm:
-
/etc/nginx/nginx.confمع إعدادات NGINX -
/etc/nginx/wallarm-status.confمع إعدادات مراقبة العقدة Wallarm. وصف مفصل متاح داخل الرابط -
/opt/wallarm/etc/collectd/wallarm-collectd.conf.d/wallarm-tarantool.confمع الإعدادات للإضافةcollectdالتي تجمع الإحصائيات من Tarantool
أدناه هناك بعض التوجيهات الأنماطية التي يمكنك تطبيقها إذا كانت بحاجة:
-
الحد من وقت معالجة الطلبات الفردية في التوجيه
wallarm_process_time_limit -
الحد من وقت الانتظار للرد من الخادم في التوجيه
proxy_read_timeout
خيارات التشغيل¶
As soon as you have the all-in one script downloaded, you can get help on it with:
Which returns:
...
Usage: setup.sh [options]... [arguments]... [filtering/postanalytics]
OPTION DESCRIPTION
-b, --batch Batch mode, non-interactive installation.
--install-only Initiates the first stage of the all-in-one installer in batch mode. Copies essential configurations, including files and binaries, and sets up NGINX for node installation, bypassing Cloud registration and activation. Requires --batch.
--skip-ngx-config Avoids automatic NGINX configuration changes that occur during the --install-only stage in batch mode, suitable for users who prefer manual adjustments later. When used with --install-only, it ensures only essential configurations are copied without altering NGINX settings. Requires --batch.
--register-only Initiates the second stage of the all-in-one installer in batch mode, completing the setup by registering the node in the Cloud and starting its service. Requires --batch.
-t, --token TOKEN Node token, required in a batch mode.
-c, --cloud CLOUD Wallarm Cloud, one of US/EU, default is EU, only used in a batch mode.
-H, --host HOST Wallarm API address, for example, api.wallarm.com or us1.api.wallarm.com, only used in a batch mode.
-P, --port PORT Wallarm API pot, for example, 443.
--no-ssl Disable SSL for Wallarm API access.
--no-verify Disable SSL certificates verification.
-f, --force If there is a node with the same name, create a new instance.
-h, --help
--version
Batch mode¶
The --batch option triggers batch (non-interactive) mode, where the script requires configuration options via the --token and --cloud flags, along with the WALLARM_LABELS environment variable if needed. In this mode, the script does not prompt the user for data input step by step as in the default mode; instead, it requires explicit commands for interaction.
Below are examples of commands to run the script in batch mode for node installation, assuming the script has already been downloaded:
Separate execution of node installation stages¶
When preparing your own machine image using the all-in-one installer for cloud infrastructure, the standard installation process outlined in this article may not suffice. Instead, you will need to execute specific stages of the all-in-one installer separately to accommodate the requirements of creating and deploying a machine image:
-
Build machine image: At this stage, it is necessary to download binaries, libraries, and configuration files of the filtering node and create a machine image based on them. Utilizing the
--install-onlyflag, the script copies the required files and modifies NGINX configurations for node operation. If you wish to make manual adjustments, you can opt to bypass the NGINX file modification by using the--skip-ngx-configflag. -
Initialize a cloud instance with cloud-init: During instance initialization, the bootstrap phase (cloud registration and service start) can be executed using cloud-init scripts. This stage can be run independently from the build phase by applying the
--register-onlyflag to the/opt/wallarm/setup.shscript copied during the build stage.
This functionality is supported starting from version 4.10.0 of the all-in-one installer in batch mode. The commands below enable the sequential execution of the outlined steps:
# If using the x86_64 version:
curl -O https://meganode.wallarm.com/6.9/wallarm-6.9.0.x86_64-glibc.sh
sudo sh wallarm-6.9.0.x86_64-glibc.sh -- --batch --install-only
sudo env WALLARM_LABELS='group=<GROUP>' /opt/wallarm/setup.sh --batch --register-only -t <TOKEN> -c US
# If using the ARM64 version:
curl -O https://meganode.wallarm.com/6.9/wallarm-6.9.0.aarch64-glibc.sh
sudo sh wallarm-6.9.0.aarch64-glibc.sh -- --batch --install-only
sudo env WALLARM_LABELS='group=<GROUP>' /opt/wallarm/setup.sh --batch --register-only -t <TOKEN> -c US
# If using the x86_64 version:
curl -O https://meganode.wallarm.com/6.9/wallarm-6.9.0.x86_64-glibc.sh
sudo sh wallarm-6.9.0.x86_64-glibc.sh -- --batch --install-only
sudo env WALLARM_LABELS='group=<GROUP>' /opt/wallarm/setup.sh --batch --register-only -t <TOKEN>
# If using the ARM64 version:
curl -O https://meganode.wallarm.com/6.9/wallarm-6.9.0.aarch64-glibc.sh
sudo sh wallarm-6.9.0.aarch64-glibc.sh -- --batch --install-only
sudo env WALLARM_LABELS='group=<GROUP>' /opt/wallarm/setup.sh --batch --register-only -t <TOKEN>
Finally, to complete the installation, you need to enable Wallarm to analyze traffic and restart NGINX.
Separate installation of filtering and postanalytics nodes¶
The filtering/postanalytics switch provides the option to install the postanalytics module separately. Without this switch, both filtering and postanalytics components are installed together by default.
API Discovery-only mode¶
You can use the node in API Discovery-only mode (available since version 5.3.7). In this mode, attacks - including those detected by the Node's built-in mechanisms and those requiring additional configuration (e.g., credential stuffing, API specification violation attempts, and malicious activity from denylisted and graylisted IPs) - are detected and blocked locally (if enabled) but not exported to Wallarm Cloud. Since there is no attack data in the Cloud, Threat Replay Testing does not work. Traffic from whitelisted IPs is allowed.
Meanwhile, API Discovery, [API session tracking][api-sessions-docs], and security vulnerability detection remain fully functional, detecting relevant security entities and uploading them to the Cloud for visualization.
This mode is for those who want to review their API inventory and identify sensitive data first, and plan controlled attack data export accordingly. However, disabling attack export is rare, as Wallarm securely processes attack data and provides sensitive attack data masking if needed.
To enable API Discovery-only mode:
-
Create or modify the
/etc/wallarm-override/env.listfile:Add the following variable:
-
Follow the node installation procedure.
With the API Discovery-only mode enabled, the /opt/wallarm/var/log/wallarm/wcli-out.log log returns the following message:
{"level":"info","component":"reqexp","time":"2025-01-31T11:59:38Z","message":"requests export skipped (disabled)"}
بدء التثبيت من جديد¶
إذا كنت بحاجة إلى حذف تثبيت العقدة Wallarm والبدء من جديد, فاتبع الخطوات أدناه.
تأثير بدء التثبيت من جديد
بدء التثبيت من جديد يشمل إيقاف وحذف الخدمات الجارية لـ Wallarm, مما يعلق تصفية الحركة حتى إعادة التثبيت. كن حذراً في بيئات الإنتاج أو الحركة الحرجة, حيث يترك الحركة غير مصفاة وعرضة للخطر.
لترقية العقدة الموجودة (مثلاً, من 4.8 إلى 4.10), راجع تعليمات الترقية.
-
إنهاء عمليات Wallarm وإزالة ملفات التكوين:
-
استمر في عملية إعادة التثبيت عن طريق اتباع تعليمات الإعداد من الخطوة الثانية.