تثبيت كوحدة ديناميكية لـ NGINX Stable¶
تصف هذه التعليمات الخطوات لتثبيت عقدة التصفية Wallarm كوحدة ديناميكية للنسخة المفتوحة المصدر من NGINX الثابتة والتي تم تثبيتها من مستودع NGINX. ستقوم العقدة بتحليل حركة المرور بشكل مباشر.
تثبيت شامل
ابتداءً من عقدة Wallarm 4.6، يوصى باستخدام التثبيت الشامل الذي يؤتمت جميع الأنشطة المدرجة في الخطوات أدناه ويجعل نشر العقدة أسهل بكثير.
حالات الاستخدام¶
Among all supported Wallarm deployment options, DEB/RPM packages for NGINX Stable is recommended for Wallarm deployment in these use cases:
-
Your infrastructure is based on bare metal or virtual machines without using container-based methods. Typically, these setups are managed with Infrastructure as Code (IaC) tools like Ansible or SaltStack.
-
Your services are built around NGINX Stable. Wallarm can extend its functionalities using these packages.
المتطلبات¶
-
Access to the account with the Administrator role in Wallarm Console for the US Cloud or EU Cloud
-
SELinux disabled or configured upon the instructions
-
NGINX version 1.24.0
Custom NGINX versions
If you have a different version, refer to the instructions on how to connect the Wallarm module to custom build of NGINX
-
Executing all commands as a superuser (e.g.
root) -
Access to
https://repo.wallarm.comto download packages. Ensure the access is not blocked by a firewall -
Access to
https://us1.api.wallarm.comfor working with US Wallarm Cloud or tohttps://api.wallarm.comfor working with EU Wallarm Cloud. If access can be configured only via the proxy server, then use the instructions -
Access to the IP addresses and their corresponding hostnames (if any) listed below. This is needed for downloading updates to attack detection rules, as well as retrieving precise IPs for your allowlisted, denylisted, or graylisted countries, regions, or data centers
-
Installed text editor vim, nano, or any other. In the instruction, vim is used
1. Install NGINX stable and dependencies¶
These are the following options to install NGINX stable from the NGINX repository:
-
Installation from the built package
sudo apt -y install curl gnupg2 ca-certificates lsb-release debian-archive-keyring echo "deb http://nginx.org/packages/debian `lsb_release -cs` nginx" | sudo tee /etc/apt/sources.list.d/nginx.list curl -fSsL https://nginx.org/keys/nginx_signing.key | sudo gpg --no-default-keyring --keyring gnupg-ring:/etc/apt/trusted.gpg.d/nginx.gpg --import sudo chmod 644 /etc/apt/trusted.gpg.d/nginx.gpg sudo apt update sudo apt -y install nginx-
Install the dependencies required for NGINX stable:
-
Install NGINX stable:
-
If an EPEL repository is added in CentOS 7.x, please disable installation of NGINX stable from this repository by adding
exclude=nginx*to the file/etc/yum.repos.d/epel.repo.Example of the changed file
/etc/yum.repos.d/epel.repo:[epel] name=Extra Packages for Enterprise Linux 7 - $basearch #baseurl=http://download.fedoraproject.org/pub/epel/7/$basearch metalink=https://mirrors.fedoraproject.org/metalink?repo=epel-7&arch=$basearch failovermethod=priority enabled=1 gpgcheck=1 gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-EPEL-7 exclude=nginx* [epel-debuginfo] name=Extra Packages for Enterprise Linux 7 - $basearch - Debug #baseurl=http://download.fedoraproject.org/pub/epel/7/$basearch/debug metalink=https://mirrors.fedoraproject.org/metalink?repo=epel-debug-7&arch=$basearch failovermethod=priority enabled=0 gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-EPEL-7 gpgcheck=1 [epel-source] name=Extra Packages for Enterprise Linux 7 - $basearch - Source #baseurl=http://download.fedoraproject.org/pub/epel/7/SRPMS metalink=https://mirrors.fedoraproject.org/metalink?repo=epel-source-7&arch=$basearch failovermethod=priority enabled=0 gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-EPEL-7 gpgcheck=1 -
Install NGINX stable from the official repository:
-
-
Compilation of the source code from the
stablebranch of the NGINX repository and installation with the same options.NGINX for AlmaLinux, Rocky Linux or Oracle Linux 8.x
This is the only option to install NGINX on AlmaLinux, Rocky Linux or Oracle Linux 8.x.
More detailed information about the NGINX installation is available in the official NGINX documentation.
2. Add Wallarm repositories¶
Wallarm node is installed and updated from the Wallarm repositories. To add repositories, use the commands for your platform:
sudo apt -y install dirmngr
curl -fSsL https://repo.wallarm.com/wallarm.gpg | sudo gpg --no-default-keyring --keyring gnupg-ring:/etc/apt/trusted.gpg.d/wallarm.gpg --import
sudo chmod 644 /etc/apt/trusted.gpg.d/wallarm.gpg
sh -c "echo 'deb https://repo.wallarm.com/debian/wallarm-node bullseye/4.8/' | sudo tee /etc/apt/sources.list.d/wallarm.list"
sudo apt update
3. Install Wallarm packages¶
The following packages are required:
-
nginx-module-wallarmfor the NGINX-Wallarm module -
wallarm-nodefor the postanalytics module, Tarantool database, and additional NGINX-Wallarm packages
4. Connect the Wallarm module¶
-
Open the file
/etc/nginx/nginx.conf: -
Ensure that the
include /etc/nginx/conf.d/*;line is added to the file. If there is no such line, add it. -
Add the following directive right after the
worker_processesdirective:Configuration example with the added directive:
-
Copy the configuration files for the system setup:
5. Connect the filtering node to Wallarm Cloud¶
The Wallarm filtering node interacts with the Wallarm Cloud. You need to connect the node to the Cloud.
When connecting node to the Cloud, you can set the node name, under which it will be displayed in the Wallarm Console UI and put the node into the appropriate node group (used to logically organize nodes in UI).
To connect the node to the Cloud, use a Wallarm token of the appropriate type:
- Open Wallarm Console → Settings → API tokens in the US Cloud or EU Cloud.
- Find or create API token with the
Node deployment/Deploymentusage type. - Copy this token.
-
Run the
register-nodescript on a machine where you install the filtering node:<TOKEN>is the copied value of the API token with theDeployrole.--labels 'group=<GROUP>'parameter puts your node to the<GROUP>node group (existing, or, if does not exist, it will be created). If you are installing filtering and postanalytics modules separately, it is recommended to put them into the same group.
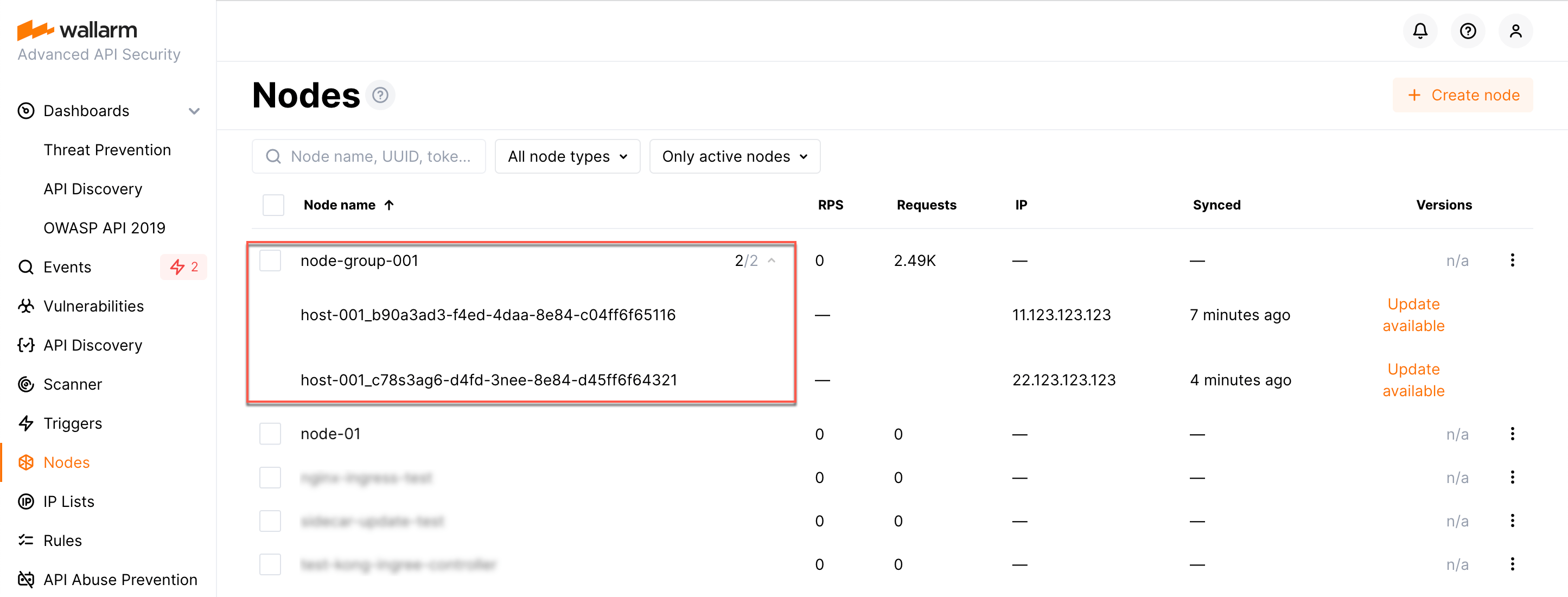
- Open Wallarm Console → Nodes in the US Cloud or EU Cloud.
- Do one of the following:
- Create the node of the Wallarm node type and copy the generated token.
- Use existing node group - copy token using node's menu → Copy token.
-
Run the
register-nodescript on a machine where you install the filtering node:
<TOKEN>is the copied value of the node token. If you are installing filtering and postanalytics modules separately, it is recommended to put them into the same group using the same node token.
- You may add
-n <HOST_NAME>parameter to set a custom name for your node instance. Final instance name will be:HOST_NAME_NodeUUID.
6. تمكين Wallarm لتحليل حركة المرور¶
By default, the deployed Wallarm Node does not analyze incoming traffic.
To enable traffic analysis and proxying of legitimate traffic, update the NGINX configuration file, typically located at /etc/nginx/sites-available/default.
The following minimal configuration adjustments are necessary:
-
Set the Wallarm Node to
wallarm_mode monitoring;. This mode is recommended for initial deployments and testing.Wallarm also supports more modes like blocking and safe blocking, which you can read more.
-
Determine where the node should forward legitimate traffic by adding the
proxy_passdirective in the required locations. This could be to the IP of an application server, a load balancer, or a DNS name. -
If present, remove the
try_filesdirective from the modified locations to ensure traffic is directed to Wallarm without local file interference.
server {
...
+ wallarm_mode monitoring;
location / {
+ proxy_pass http://example.com;
- # try_files $uri $uri/ =404;
}
...
}
7. إعادة تشغيل NGINX¶
Providing user with root permission
If you are running NGINX as a user that does not have root permission, then add this user to the wallarm group using the following command:
where <user_name> is the name of the user without root permission.
8. تكوين إرسال حركة المرور إلى عقدة Wallarm¶
Update targets of your load balancer to send traffic to the Wallarm instance. For details, please refer to the documentation on your load balancer.
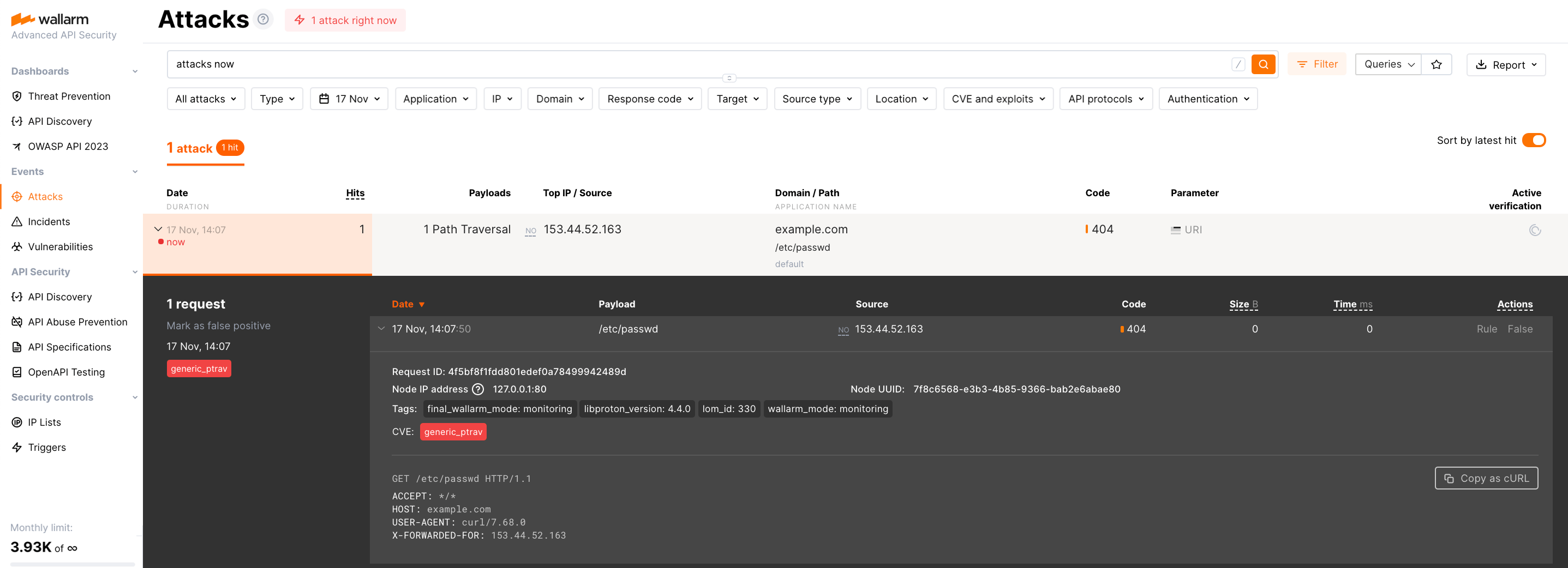
9. اختبار تشغيل عقدة Wallarm¶
-
Send the request with test Path Traversal attack to a protected resource address:
If traffic is configured to be proxied to
example.com, include the-H "Host: example.com"header in the request. -
Open Wallarm Console → Attacks section in the US Cloud or EU Cloud and make sure the attack is displayed in the list.
-
Optionally, test other aspects of the node functioning.
10. ضبط الحل المنشور بدقة¶
تم تثبيت الوحدة الديناميكية Wallarm بالإعدادات الافتراضية لـ NGINX الثابتة. قد تتطلب عقدة التصفية بعض الإعدادات الإضافية بعد النشر.
يتم تحديد إعدادات Wallarm باستخدام توجيهات NGINX أو واجهة Wallarm Console. يجب ضبط التوجيهات في الملفات التالية على الجهاز مع عقدة Wallarm:
-
/etc/nginx/conf.d/default.confمع إعدادات NGINX -
/etc/nginx/conf.d/wallarm.confمع إعدادات عقدة التصفية العامةيُستخدم الملف للإعدادات المطبقة على جميع النطاقات. لتطبيق إعدادات مختلفة على مجموعات نطاقات مختلفة، استخدم الملف
default.confأو أنشئ ملفات تكوين جديدة لكل مجموعة نطاقات (على سبيل المثال،example.com.confوtest.com.conf). المعلومات أكثر تفصيلاً حول ملفات تكوين NGINX متاحة في الوثائق الرسمية لـ NGINX. -
/etc/nginx/conf.d/wallarm-status.confمع إعدادات مراقبة عقدة Wallarm. الوصف التفصيلي متاح في الرابطlink -
/etc/default/wallarm-tarantoolأو/etc/sysconfig/wallarm-tarantoolمع إعدادات قاعدة البيانات Tarantool
أدناه هناك بعض من الإعدادات النموذجية التي يمكنك تطبيقها إذا لزم الأمر:
-
Using the balancer of the proxy server behind the filtering node
-
Limiting the single request processing time in the directive
wallarm_process_time_limit -
Limiting the server reply waiting time in the NGINX directive
proxy_read_timeout -
Limiting the maximum request size in the NGINX directive
client_max_body_size
القيود¶
- كشف التقديم الاعتمادي غير مدعوم حاليًا، حيث لم يتم تحديث الحزم إلى إصدار 4.10 بعد.