Wallarm API overview¶
Wallarm API provides interaction between components of the Wallarm system. You can use Wallarm API methods to create, get, or update the following instances:
-
vulnerabilities
-
attacks
-
incidents
-
users
-
clients
-
filter nodes
-
etc.
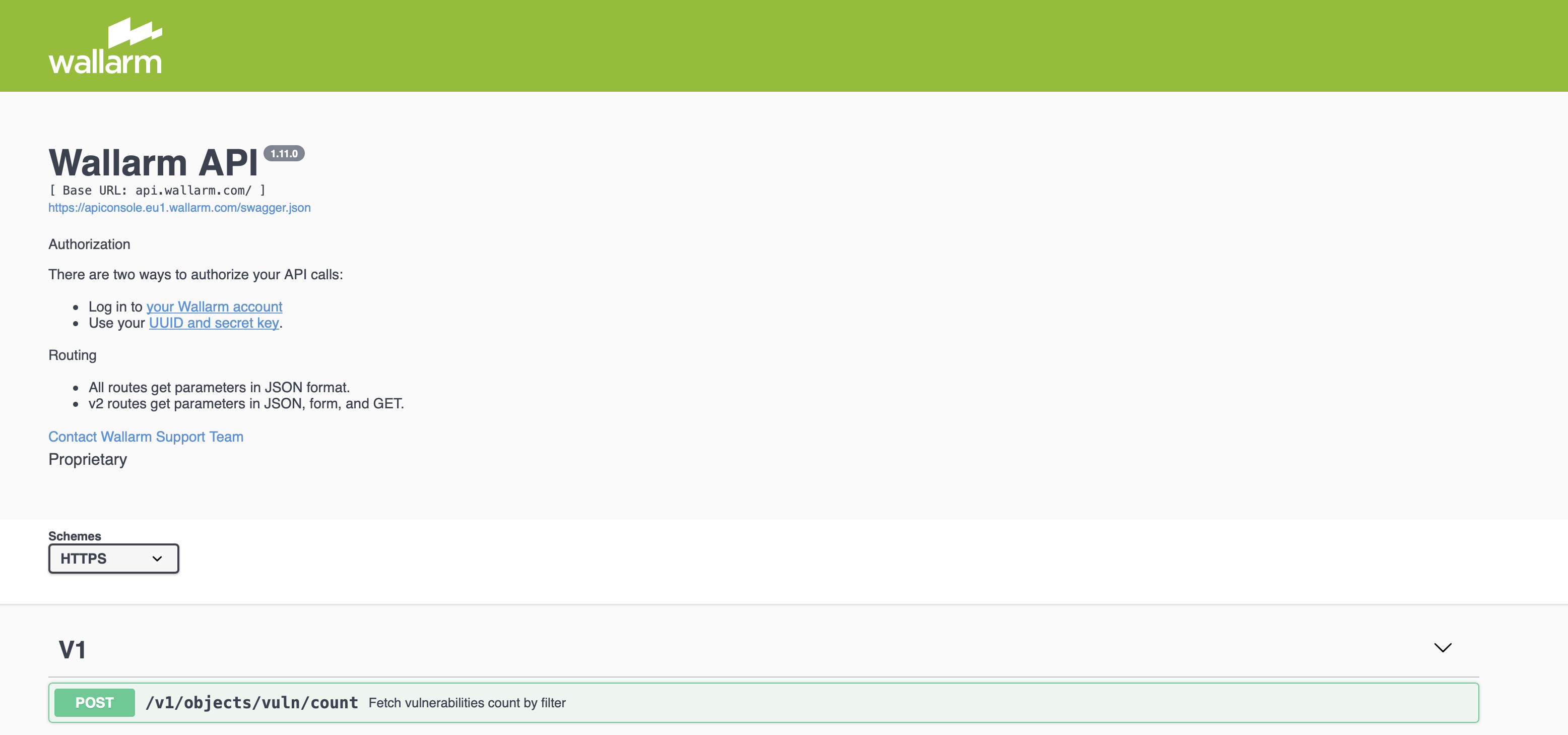
Description of API methods is given in the Wallarm API Console available from Wallarm Console → top right → ? → Wallarm API Console or directly by the link:
API endpoint¶
API requests are sent to the following URL:
-
https://us1.api.wallarm.com/for the US cloud -
https://api.wallarm.com/for the EU cloud -
https://me1.api.wallarm.com/for the ME cloud
Authentication of API requests¶
You must be a verified user to make Wallarm API requests. The method of API requests authentication depends on the client sending the request:
Wallarm API Console¶
A token is used for request authentication. The token is generated after successful authentication in your Wallarm account.
-
Sign in to your Wallarm Console using the link:
- https://us1.my.wallarm.com/ for the US cloud
- https://my.wallarm.com/ for the EU cloud
- https://me1.my.wallarm.com/ for the ME cloud
-
Refresh the Wallarm API Console page using the link:
- https://apiconsole.us1.wallarm.com/ for the US cloud
- https://apiconsole.eu1.wallarm.com/ for the EU cloud
- https://apiconsole.me1.wallarm.com/ for the ME cloud
-
Go to the required API method → the Try it out section, input parameter values, and Execute the request.
Your own API client¶
To authenticate requests from your own API client to Wallarm API:
-
Sign in to your Wallarm account in the US Cloud, EU Cloud, or ME Cloud → Settings → API tokens.
-
Create token to access the Wallarm API.
-
Open your token and copy value from the Token section.
-
Send the required API request passing the Token value in the
X-WallarmApi-Tokenheader parameter.
Wallarm approach to API development and documentation¶
Wallarm API Reference is a single page application (SPA) with all displayed data being dynamically fetched from the API. This design drives Wallarm to use the API-first approach when new data and functionality is initially made available in the public API and as the next step is described in the API Reference. Normally all new functionality is released in parallel in both public API and API Reference, but sometimes new API changes are released ahead of API Reference changes, and some functionality is available via the public API only.
Wallarm API Reference is generated from the Swagger file using the Swagger UI tool. API Reference provides an easy way to learn about available API endpoints, methods, and data structures. It also provides a simple way to try all available endpoints.