API Specification Enforcement Setup  ¶
¶
This article describes how to enable and configure your API protection based on your uploaded API specification.
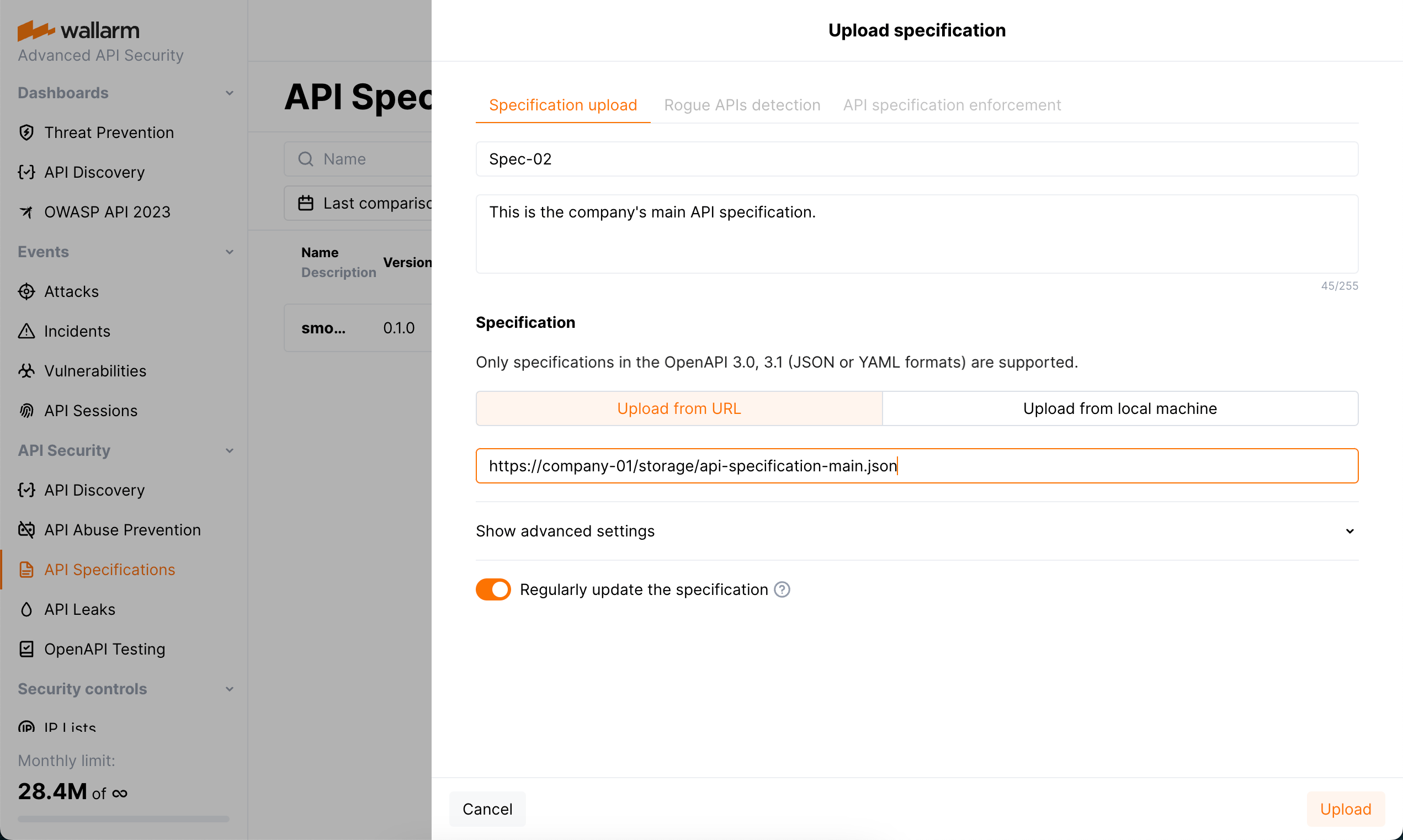
Step 1: Upload specification¶
You can upload only specifications in the OpenAPI 3.0, 3.1 (JSON or YAML formats):
-
In the API Specifications section in US Cloud or EU Cloud, or ME Cloud, click Upload specification.
OAS 3.1 requires NGINX Node 6.6.1+ or or Native Node 0.20.0+.
-
Set specification upload parameters and start uploading.
Specification file is checked for correspondence to the API specification syntax, and if not valid, is not uploaded. Note that you will not be able to start configuring API specification enforcement, until the specification file is successfully uploaded.
If you select to upload specification from URI and select the Regularly update the specification (every hour) option, there may be errors during regular update: URI can be unavailable or updated specification file may not correspond to the API specification syntax. To get notifications on such errors, in your configured Integrations, select the System related events—notifications about specification upload errors is included into this category.
Step 2: Set actions for violations of policies¶
-
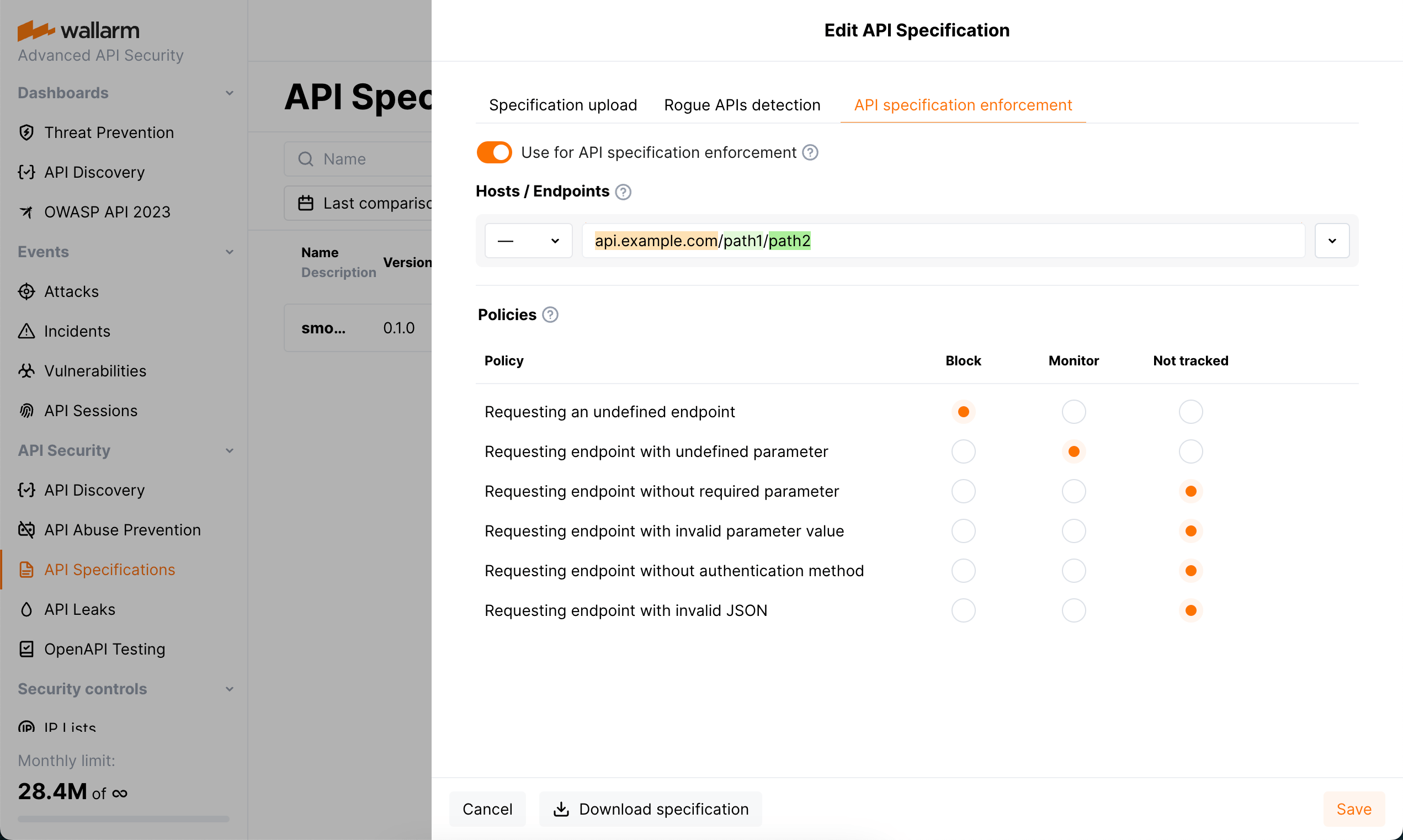
Click the API specification enforcement tab.
Rogue API detection
- Besides applying security policies, specifications may be used by API Discovery module for the rogue API detection. The tab is displayed if API Discovery is enabled.
- Before using the specification for applying security policies, it is recommended to use it for searching the rogue (shadow and zombie) APIs using API Discovery. This way you will be able to understand how much your specification differs from the actual requests of your clients - these differences will most probably cause blocking related requests after applying security policies.
-
Select Use for API specification enforcement.
-
Specify host or endpoint for which you want to activate policy violation actions.
- Note that if you incorrectly specify to which endpoints the uploaded specification should be applied, there will be many false positive events.
- If you have several specifications that apply to the same host, but to different endpoints (for example
domain.com/v1/api/users/anddomain.com/v1/api/orders/), you must indicate to which endpoints the specification should be applied. - If you add a specification to a host, and then add another specification to individual endpoints of this host, both specifications will be applied to these endpoints.
- The value can be configured via the URI constructor or advanced edit form.
-
Set how the system should react if requests violate your specification.
Details on possible violations:
- Requesting an undefined endpoint - a request targets the endpoint not presented in your specification
- Requesting endpoint with undefined parameter - a request contains the parameter not presented for this endpoint in your specification
- Requesting endpoint without required parameter - a request does not contain the parameter or its value that are marked as required in your specification
- Requesting endpoint with invalid parameter value - a request parameter's value in not in correspondence with its type/format defined by your specification
- Requesting endpoint without authentication method - a request does not contain the information about the authentication method
- Requesting endpoint with invalid JSON - a request contains a JSON object not in correspondence with the schema object in specification that defines the structure and rules for the JSON data expected
The system can perform the following actions in case of found inconsistency:
-
Block - block a request and put in the Attacks section as blocked
Filtration mode
The Wallarm node will block requests only when the blocking filtration mode is enabled for target endpoint - otherwise, Monitor action will be performed.
-
Monitor - mark a request as incorrect, but do not block, put it in the Attacks section as monitored
- Not tracked - do nothing
Note that several specifications can be used for setting policies. In case when one request falls on two different specifications (the same policy and different actions in different specifications), the following will happen:
- Block and Block - the request will be blocked and two events will be added to the Attacks section with status
Blockedpointing at the reason of blocking and at the fact that the request violated two different specifications. - Monitor and Block - the request will be blocked and one event will be added to the Attacks section with status
Blockedexplaining the reason of blocking. - Monitor and Monitor - the request will not be blocked and two events will be added to the Attacks section with status
Monitoringpointing at the fact that specific policy was violated.
When using the specification for setting security policies for the first time, it is recommended to set
Monitoras a reaction to make sure that the specification is applied to the necessary endpoints and detects real errors.
Disabling¶
API Specification Enforcement's work is based on uploaded specification or several specifications each having the Use for API specification enforcement option selected. Consider that unchecking this option for some specification or deleting this specification will result in stopping protection based on this specification.
Also, in some cases that may be necessary to disable the API Specification Enforcement functionality only for some parts of your API. This can be done:
-
For all-in-one installer deployments, for any
serversection where API Specification Enforcement is used by means of thewallarm_enable_apifwNGINX directive set tooff. -
For NGINX-based Docker image, by means of the
WALLARM_APIFW_ENABLEenvironment variable set tofalse. -
For NGINX Ingress Controller, by means of the
controller.wallarm.apifirewallvalues group withenableset tofalse.