Deploying NGINX Ingress Controller with Integrated Wallarm Services¶
Community-based NGINX Ingress Controller — end of support
Official support of the Community-based NGINX Ingress Controller ends in April 2026. This controller will remain functional but will no longer receive updates, bug fixes, or security patches.
Wallarm has released a new Ingress Controller based on the F5 NGINX Ingress Controller. We strongly recommend migrating to this version for continued support and security updates.
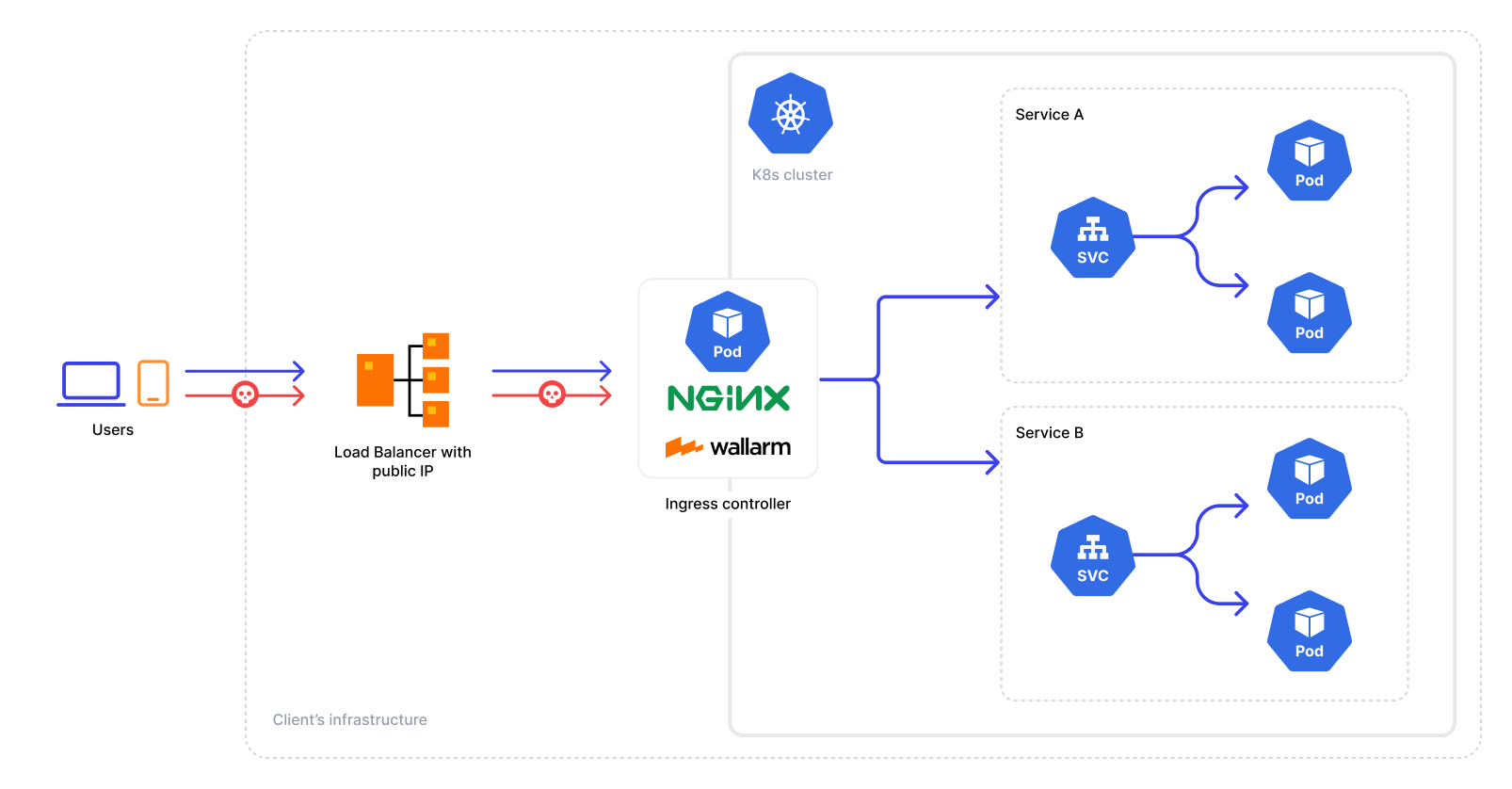
These instructions provide you with the steps to deploy the Wallarm NGINX-based Ingress controller to your K8s cluster. The solution is deployed from the Wallarm Helm chart.
The solution is built on the Community Ingress NGINX Controller with integrated Wallarm services. The latest version uses Community Ingress NGINX Controller 1.15.0 with NGINX stable 1.27.1, the upstream Helm chart 4.15.0, and Alpine Linux 3.23.3 as the base image.
It has the following architecture:
Use cases¶
Among all supported Wallarm deployment options, this solution is the recommended one for the following use cases:
-
There is no Ingress controller and security layer routing traffic to Ingress resources compatible with Community Ingress NGINX Controller.
-
You are currently using the Community Ingress NGINX Controller and are in search of a security solution that offers both the standard controller functionality and enhanced security features. In this case, you can effortlessly switch to the Wallarm-NGINX Ingress Controller detailed in these instructions. Simply migrate your existing configuration to a new deployment to complete the replacement.
For simultaneous use of both the existing Ingress controller and the Wallarm controller, refer to the Ingress Controller chaining guide for configuration details.
Requirements¶
-
Kubernetes platform version 1.31-1.35
-
Helm package manager
-
Compatibility of your services with the Community Ingress NGINX Controller version 1.15.0
-
Access to the account with the Administrator role in Wallarm Console for the US Cloud or EU Cloud
-
Access to the Wallarm API host for your Cloud:
https://us1.api.wallarm.com,https://api.wallarm.com, orhttps://me1.api.wallarm.com -
Access to
https://charts.wallarm.comto add the Wallarm Helm charts. Ensure the access is not blocked by a firewall -
Access to the Wallarm repositories on Docker Hub
https://hub.docker.com/r/wallarm. Make sure the access is not blocked by a firewall -
Access to the IP addresses and their corresponding hostnames (if any) listed below. This is needed for downloading updates to attack detection rules and API specifications, as well as retrieving precise IPs for your allowlisted, denylisted, or graylisted countries, regions, or data centers
See also
Known restrictions¶
-
Operation without the postanalytics module is not supported.
-
Scaling down postanalytics module may result in a partial loss of attack data.
Installation¶
-
Install the Wallarm Ingress controller.
-
Enable traffic analysis for your Ingress.
-
Check the Wallarm Ingress controller operation.
Step 1: Installing the Wallarm Ingress Controller¶
To install the Wallarm Ingress Controller:
-
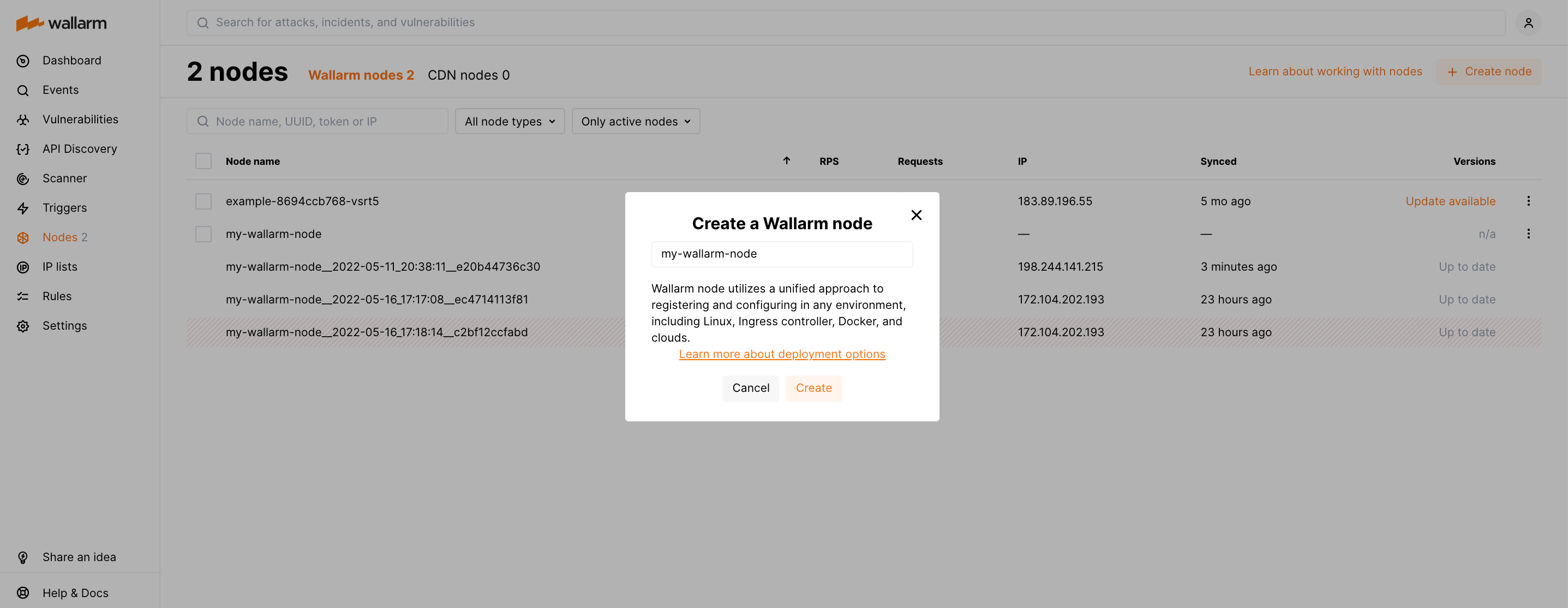
Generate a filtering node token of the appropriate type:
-
Create a Kubernetes namespace to deploy the Helm chart with the Wallarm Ingress controller:
-
Add the Wallarm chart repository:
-
Create the
values.yamlfile with the Wallarm configuration. Example of the file with the minimum configuration is below.When using an API token, specify a node group name in the
nodeGroupparameter. Your node will be assigned to this group, shown in the Wallarm Console's Nodes section. The default group name isdefaultIngressGroup.You can also store the Wallarm node token in Kubernetes secrets and pull it to the Helm chart. Read more
Deployment from your own registries
You can overwrite elements of the
values.yamlfile to install the Wallarm Ingress controller from the images stored in your own registries. -
Install the Wallarm packages:
helm install --version 6.12.0 <RELEASE_NAME> wallarm/wallarm-ingress -n <KUBERNETES_NAMESPACE> -f <PATH_TO_VALUES><RELEASE_NAME>is the name for the Helm release of the Ingress controller chart<KUBERNETES_NAMESPACE>is the Kubernetes namespace you have created for the Helm chart with the Wallarm Ingress controller<PATH_TO_VALUES>is the path to thevalues.yamlfile
Step 2: Enabling traffic analysis for your Ingress¶
kubectl annotate ingress <YOUR_INGRESS_NAME> -n <YOUR_INGRESS_NAMESPACE> nginx.ingress.kubernetes.io/wallarm-mode=monitoring
kubectl annotate ingress <YOUR_INGRESS_NAME> -n <YOUR_INGRESS_NAMESPACE> nginx.ingress.kubernetes.io/wallarm-application="<APPLICATION_ID>"
-
<YOUR_INGRESS_NAME>is the name of your Ingress -
<YOUR_INGRESS_NAMESPACE>is the namespace of your Ingress -
<APPLICATION_ID>is a positive number that is unique to each of your applications or application groups. This will allow you to obtain separate statistics and to distinguish between attacks aimed at the corresponding applications
Step 3: Checking the Wallarm Ingress Controller operation¶
-
Get the list of pods:
The Wallarm pod status should be STATUS: Running and READY: N/N:
-
Send the request with the test Path Traversal attack to the Ingress Controller Service:
If the filtering node is working in the
blockmode, the code403 Forbiddenwill be returned in the response to the request and the attack will be displayed in Wallarm Console → Attacks.
ARM64 deployment¶
With the NGINX Ingress controller's Helm chart version 4.8.2, ARM64 processor compatibility is introduced. Initially set for x86 architectures, deploying on ARM64 nodes involves modifying the Helm chart parameters.
In ARM64 settings, Kubernetes nodes often carry an arm64 label. To assist the Kubernetes scheduler in allocating the Wallarm workload to the appropriate node type, reference this label using nodeSelector, tolerations, or affinity rules in the Wallarm Helm chart configuration.
Below is the Wallarm Helm chart example for Google Kubernetes Engine (GKE), which uses the kubernetes.io/arch: arm64 label for relevant nodes. This template is modifiable for compatibility with other cloud setups, respecting their ARM64 labeling conventions.
controller:
nodeSelector:
kubernetes.io/arch: arm64
admissionWebhooks:
nodeSelector:
kubernetes.io/arch: arm64
patch:
nodeSelector:
kubernetes.io/arch: arm64
wallarm:
postanalytics:
nodeSelector:
kubernetes.io/arch: arm64
enabled: true
token: "<NODE_TOKEN>"
apiHost: "us1.api.wallarm.com" # if using EU Cloud, comment out this line; if using ME Cloud, set to "me1.api.wallarm.com"
# If using an API token, uncomment the following line and specify your node group name
# nodeGroup: defaultIngressGroup
controller:
tolerations:
- key: kubernetes.io/arch
operator: Equal
value: arm64
effect: NoSchedule
admissionWebhooks:
patch:
tolerations:
- key: kubernetes.io/arch
operator: Equal
value: arm64
effect: NoSchedule
wallarm:
postanalytics:
tolerations:
- key: kubernetes.io/arch
operator: Equal
value: arm64
effect: NoSchedule
enabled: true
token: "<NODE_TOKEN>"
apiHost: "us1.api.wallarm.com" # if using EU Cloud, comment out this line; if using ME Cloud, set to "me1.api.wallarm.com"
# If using an API token, uncomment the following line and specify your node group name
# nodeGroup: defaultIngressGroup
Deployment from your own registries¶
If you cannot pull the Docker images from the Wallarm public repository due to some reasons, for example because you company security policy restricts usage of any external resources, instead you can:
-
Clone these images to your private registry.
-
Install Wallarm NGINX-based Ingress controller using them.
The following Docker images are used by the Helm chart for NGINX-based Ingress Controller deployment:
To install Wallarm NGINX-based Ingress controller using images stored in your registry, overwrite the values.yaml file of Wallarm Ingress controller Helm chart:
controller:
image:
## The image and tag for wallarm nginx ingress controller
##
registry: <YOUR_REGISTRY>
image: wallarm/ingress-controller
tag: <IMAGE_TAG>
wallarm:
helpers:
## The image and tag for the helper image
##
image: <YOUR_REGISTRY>/wallarm/node-helpers
tag: <IMAGE_TAG>
Then run installation using your modified values.yaml.
Security Context Constraints (SCC) in OpenShift¶
When deploying the NGINX Ingress Controller on OpenShift, it is necessary to define a custom Security Context Constraint (SCC) to suit the security requirements of the platform. The default constraints may be insufficient for the Wallarm solution, potentially leading to errors.
Below is the recommended custom SCC for the Wallarm NGINX Ingress Controller.
Apply the SCC before deploying the controller
Ensure the SCC is applied prior to deploying the Wallarm NGINX Ingress controller.
-
Define the custom SCC in the
wallarm-scc.yamlfile as follows:--- allowHostDirVolumePlugin: false allowHostIPC: false allowHostNetwork: false allowHostPID: false allowHostPorts: false allowPrivilegeEscalation: false allowPrivilegedContainer: false allowedCapabilities: - NET_BIND_SERVICE apiVersion: security.openshift.io/v1 defaultAddCapabilities: null fsGroup: type: MustRunAs groups: [] kind: SecurityContextConstraints metadata: annotations: kubernetes.io/description: wallarm-ingress-admission provides features similar to restricted-v2 SCC but pins user id to 65532 and is more restrictive for volumes name: wallarm-ingress-admission priority: null readOnlyRootFilesystem: false requiredDropCapabilities: - ALL runAsUser: type: MustRunAs uid: 65532 seLinuxContext: type: MustRunAs seccompProfiles: - runtime/default supplementalGroups: type: RunAsAny users: [] volumes: - projected --- allowHostDirVolumePlugin: false allowHostIPC: false allowHostNetwork: false allowHostPID: false allowHostPorts: false allowPrivilegeEscalation: false allowPrivilegedContainer: false allowedCapabilities: - NET_BIND_SERVICE apiVersion: security.openshift.io/v1 defaultAddCapabilities: null fsGroup: type: MustRunAs groups: [] kind: SecurityContextConstraints metadata: annotations: kubernetes.io/description: wallarm-ingress-controller provides features similar to restricted-v2 SCC but pins user id to 101 and is a little more restrictive for volumes name: wallarm-ingress-controller priority: null readOnlyRootFilesystem: false requiredDropCapabilities: - ALL runAsUser: type: MustRunAs uid: 101 seLinuxContext: type: MustRunAs seccompProfiles: - runtime/default supplementalGroups: type: RunAsAny users: [] volumes: - configMap - secret - emptyDir -
Apply this policy to a cluster:
-
Create a Kubernetes namespace where the NGINX Ingress controller will be deployed, e.g.:
-
Allow the Wallarm Ingress controller workloads to use this SCC policy:
oc adm policy add-scc-to-user wallarm-ingress-admission \ -z <RELEASE_NAME>-wallarm-ingress-admission -n wallarm-ingress oc adm policy add-scc-to-user wallarm-ingress-controller \ -z <RELEASE_NAME>-wallarm-ingress -n wallarm-ingress oc adm policy add-scc-to-user wallarm-ingress-controller \ -z default -n wallarm-ingress<RELEASE_NAME>: Helm release name that you will use duringhelm install.-n wallarm-ingress: namespace where the NGINX Ingress controller will be deployed (created above).
For example, with the namespace
wallarm-ingressand the Helm release namewlrm-ingress:oc adm policy add-scc-to-user wallarm-ingress-admission \ -z wlrm-ingress-wallarm-ingress-admission -n wallarm-ingress oc adm policy add-scc-to-user wallarm-ingress-controller \ -z wlrm-ingress-wallarm-ingress -n wallarm-ingress oc adm policy add-scc-to-user wallarm-ingress-controller \ -z default -n wallarm-ingress -
Deploy the Wallarm NGINX Ingress controller using the same namespace and Helm release name specified above.
-
Verify that the correct SCC is applied to Wallarm pods:
WALLARM_INGRESS_NAMESPACE="<WALLARM_INGRESS_NAMESPACE>" POD=$(kubectl -n ${WALLARM_INGRESS_NAMESPACE} get pods -o name -l "app.kubernetes.io/component=controller" | cut -d '/' -f 2) kubectl -n ${WALLARM_INGRESS_NAMESPACE} get pod ${POD} -o jsonpath='{.metadata.annotations.openshift\.io\/scc}{"\n"}' WALLARM_INGRESS_NAMESPACE="<WALLARM_INGRESS_NAMESPACE>" POD=$(kubectl -n ${WALLARM_INGRESS_NAMESPACE} get pods -o name -l "app.kubernetes.io/component=controller-wallarm-wstore" | cut -d '/' -f 2) kubectl -n ${WALLARM_INGRESS_NAMESPACE} get pod ${POD} -o jsonpath='{.metadata.annotations.openshift\.io\/scc}{"\n"}'The expected output is
wallarm-ingress-controller.
Configuration¶
After the Wallarm Ingress controller is successfully installed and checked, you can make advanced configurations to the solution such as:
To find parameters used for advanced configuration and appropriate instructions, please follow the link.